"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
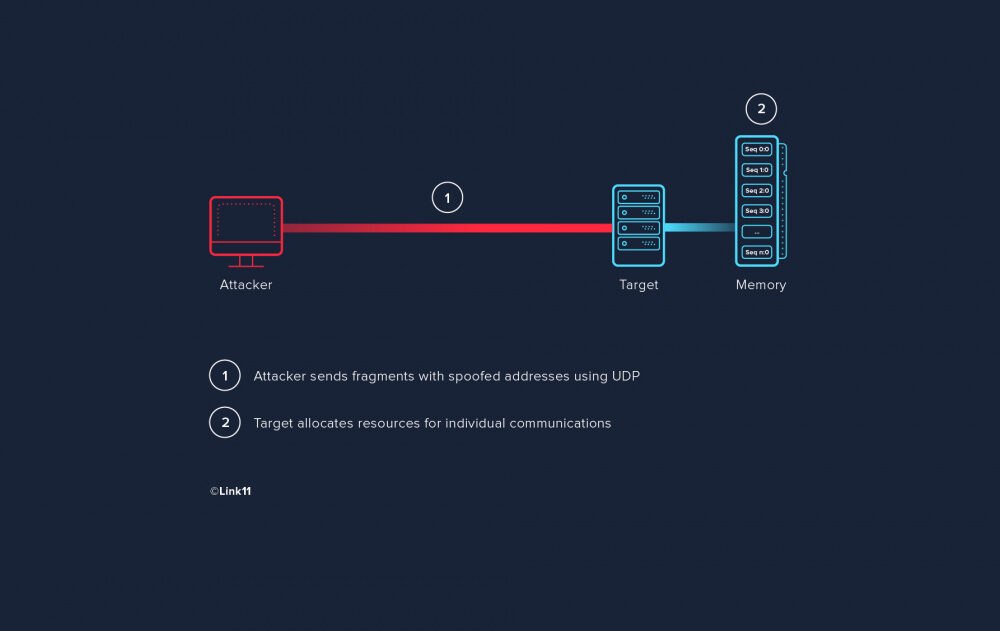
A Fragment Overlap Attack, also known as an IP Fragmentation Attack, is an attack that is based on how...
Read more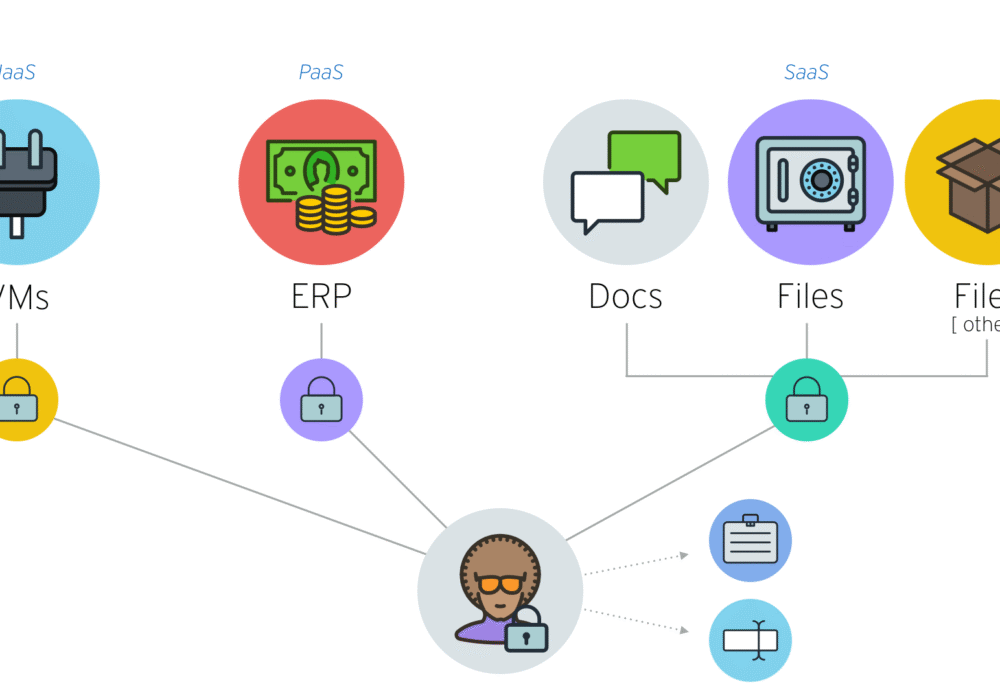
An Infrastructure as a Service (IaaS) is a cloud based service that helps companies build and manage...
Read more
A Platform as a Service (PaaS) is a type of cloud computing, similar to Software as a Service (SaaS),...
Read more
Barbara Corcoran, a world famous Shark Tank host, was scammed out of nearly $400,000 in late February....
Read more
Steganography (pronounced: steh·guh·naa·gruh·fee) is the technique of hiding data secretly within an...
Read more
Software as a Service (SaaS) is a cloud-based service where instead of downloading software to your...
Read more
This video outlines how an MSP or Client admin can download and customize CyberHoot cybersecurity template...
Read more
Human-Machine Interface (HMI) is the hardware or software through which an operator interacts with a...
Read more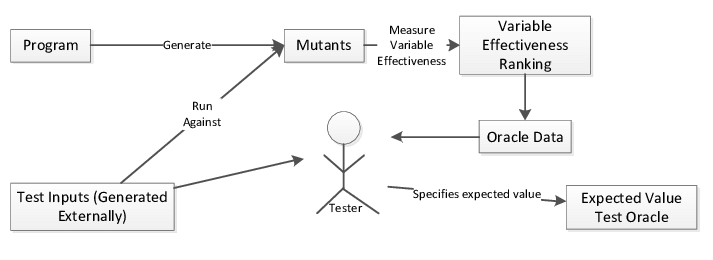
A Test Oracle is a mechanism for determining whether the program has passed or failed a test. The use...
Read more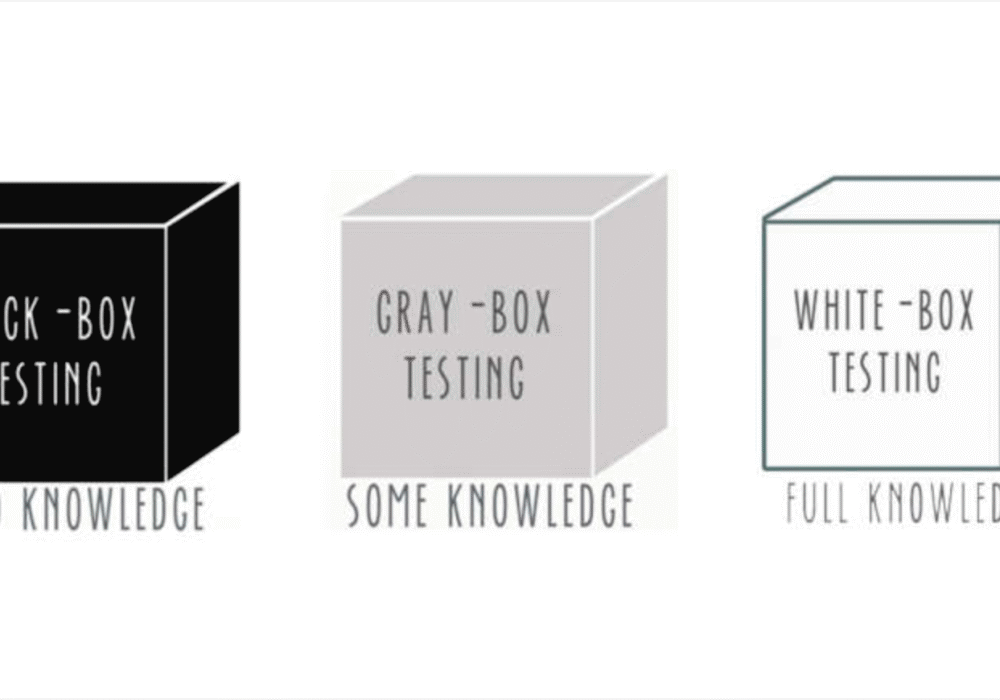
Black Box Testing is a method of software testing that examines the functionality of an application...
Read more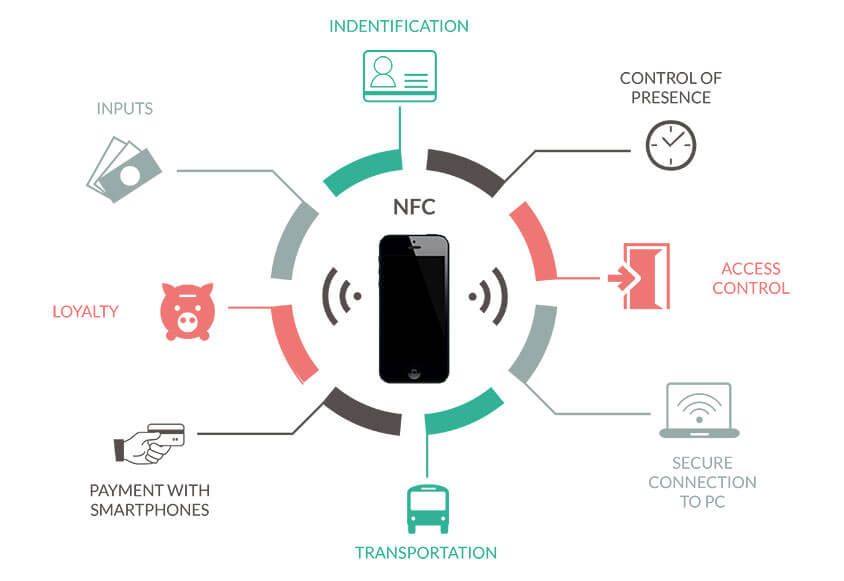
Near Field Communications (NFC) is a short-range wireless technology that enables simple and secure...
Read more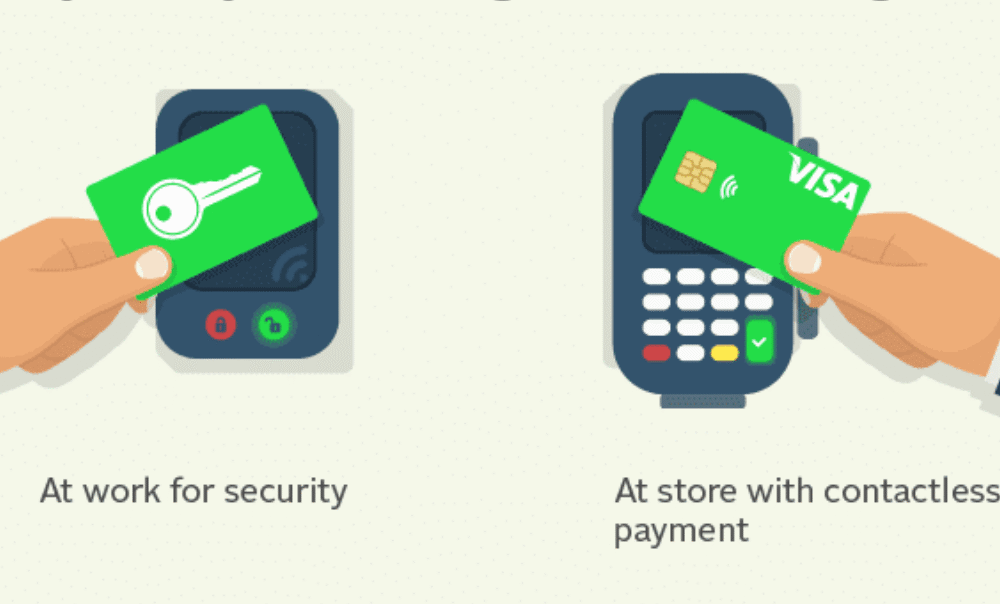
Radio Frequency IDentification (RFID) is a system used to track objects, people, or animals using tags...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
