“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”
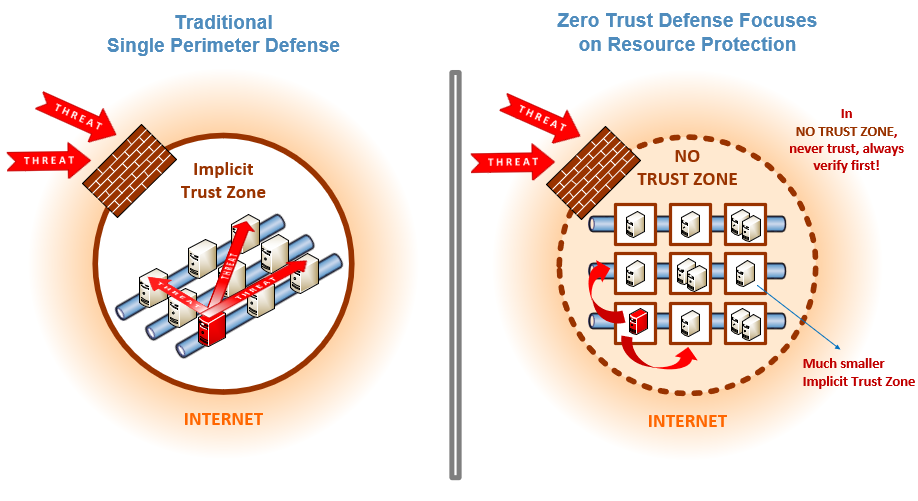
Zero Trust is a security strategy focused on the belief that organizations shouldn't automatically...
Read more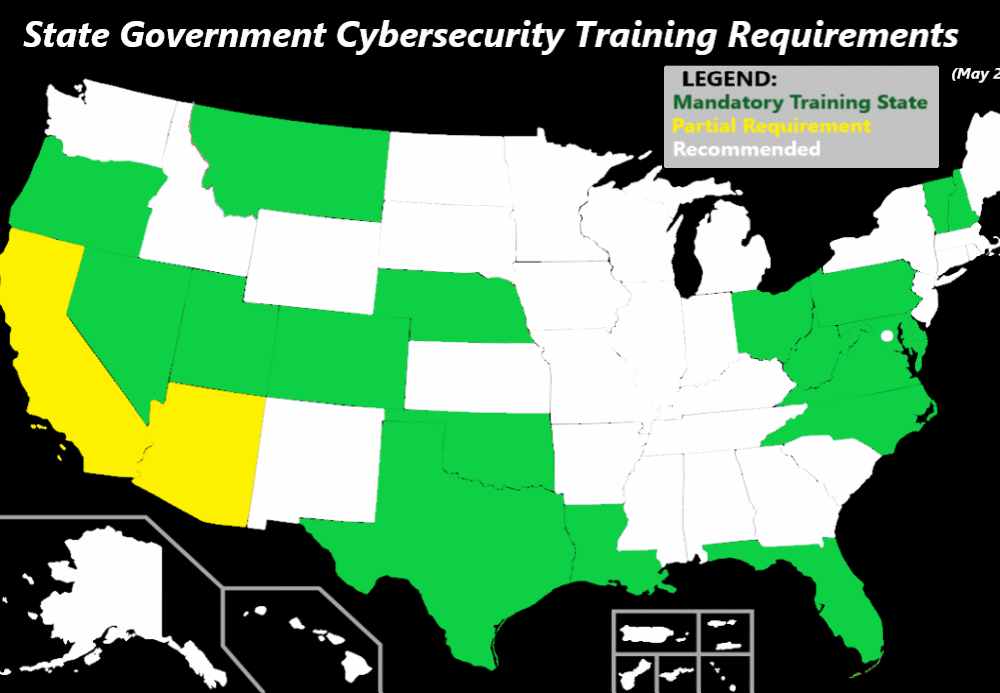
May 17, 2021: Following the Ransomware Attack on the Colonial Pipeline, Texas Governor Greg Abbott took...
Read more
The Ransomware Task Force (RTF) is a group of high-profile security vendors who teamed up with the...
Read more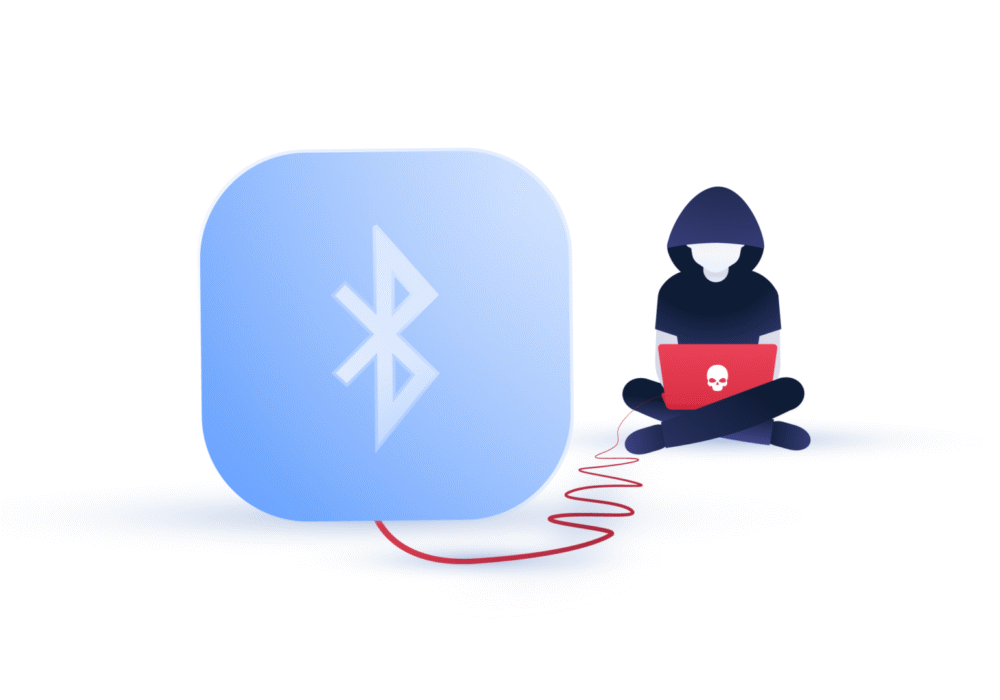
Bluejacking is the unauthorized sending of messages from one Bluetooth device to another. Bluetooth is...
Read more
The United States' largest pipeline, Colonial Pipeline, halted operations due to a ransomware attack. Colonial...
Read more
May 4th, 2021: Apple has released IOS updates for 4 critical issues that impact all Mac, iOS, iPad, and...
Read more
Security researchers in Germany have put out a press release about research findings to be presented at...
Read more
It's apparent that ransomware and its evolution into leakware is a critical threat to most businesses...
Read more
Threat Intelligence (TI) is information about current attack tactics and techniques (T&T) used by...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
