A Script is a list of commands that are executed by a certain program or scripting engine. Scripts may be used to automate processes on a local computer or to generate web pages on the Internet. For example, Disk Operating System (DOS) scripts and Visual Basic (VB) Scripts may be used to run processes on Windows machines, while AppleScript scripts can automate tasks on Macs. ASP, JSP, PHP, and Microsoft PowerShell scripts are often run on servers to generate dynamic web page content.
Script files are usually text documents that contain instructions written in a scripting language. This means most scripts can be opened and edited using a basic text editor. However, when opened by the appropriate scripting engine, the commands within the script are executed. Visual Basic (VB) scripts, for example, will run when double-clicked, using Windows’ built-in VB scripting support. Since VB scripts can access and modify local files, you should never run a VB script that you receive as an unknown e-mail attachment.
Script languages are generally easier and faster to code in than the more structured and compiled languages such as C and C++. However, a script takes longer to run than a compiled program since each instruction is being handled by another program first (requiring additional instructions) rather than directly by the basic instruction processor. [Editors note: compiled languages are also an interpretation or abstraction from what is called Assembly Language. Assembly language is the code that interacts with the bare hardware of your computer – the CPU, memory, storage systems.]
Not many business owners need to be familiar with and use scripts; however, your IT professionals should be able to. Computers have been designed from the beginning to do what is difficult for humans, repeat processes over and over millions and billions of times faster than humans can. Scripts are one level of such automation and can be handy for automating your business processes on occasion. Cybersecurity professionals also like to use scripts to automate many things like security testing, scanning, data manipulation, and searching for needles in haystacks. Speaking of security professionals, CyberHoot likes to remind you of the following important security measures every business must take to protect themselves with a robust cybersecurity program.
The following recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
Each of these recommendations, except cyber-insurance, is built into CyberHoot’s product and virtual Chief Information Security Officer services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
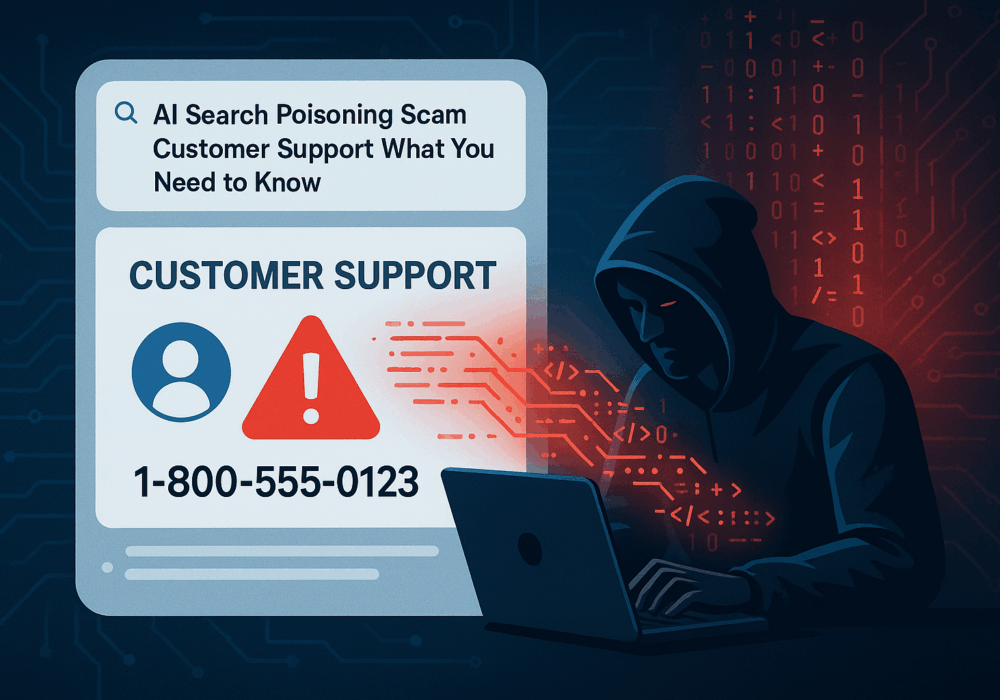
Cybercriminals always follow Internet eyeballs. Not literally, but figuratively. And today's eyeballs are...
Read more
Active Attacks on Messaging Apps The Cybersecurity and Infrastructure Security Agency (CISA) recently issued...
Read more
The world of work has changed enormously since COVID-19. Gone are the days when IT admins sat behind a corporate...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
