A Self Assessment Questionnaire (SAQ) is most commonly used in the Payment Card Industry Data Security Standard (PCI-DSS) space to determine if a merchant or service provider is compliant with PCI-DSS standards. There are 8 different SAQ types, each for different types of organizations that handle PCI information. The 8 different types can be found below:
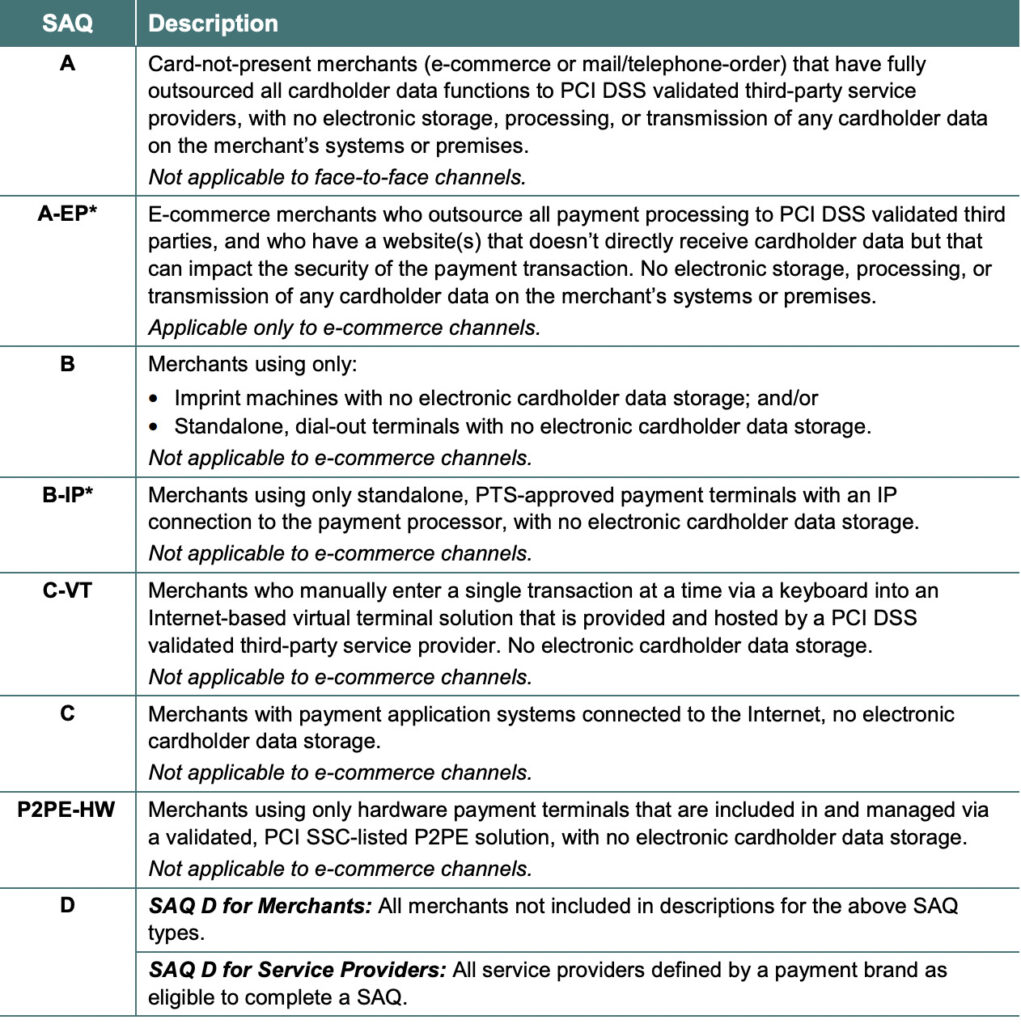
How you process credit cards and handle cardholder data determines which SAQ your business needs to fill out. For example, if you don’t have a storefront and all your products are sold online through a third party, you probably qualify for SAQ A or SAQ A-EP. If you do have a storefront that processes credit cards through the Internet and you also store customer credit card data, you’re probably an SAQ D merchant.
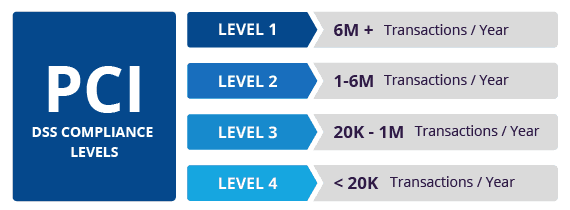
Beyond completing an SAQ for your PCI compliance needs, there is a secondary metric SMBs should consider – namely transaction volumes. PCI-DSS also has ranges of transaction volumes that dictate whether you can self-assess (below 20,000 credit card transactions a year) and must hire an outside QSA (Qualified Security Assessor) where you are Level 2 or Level 1 compliance level, to perform an audit of your company.
The SAQ or Self-Assessment Questionnaire isn’t just a roadmap to compliance; it’s a roadmap to better cybersecurity. Filling out a PCI SAQ is one of the best ways to make sure you aren’t missing any business security requirements. In addition, merchant processors don’t want to work with insecure businesses, so they typically require each merchant to provide a PCI SAQ as proof of payment security. If your organization works with PCI data, then you likely have completed or need to complete an SAQ, reference the table above for which SAQ is applicable to your business. Working through your SAQ will help you determine what you should be doing, but the information below will help you improve your cybersecurity hygiene even further.
Additional Cybersecurity Recommendations
Additionally, these recommendations below will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
All of these recommendations are built into CyberHoot the product or CyberHoot’s vCISO Services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Additional Reading:
MSPs Should Require Risk Assessments
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
For years, organizations have relied on fake email phishing simulations to measure employee resilience to...
Read more
Welcome to our two-part blog series on Microsoft’s new email security enhancement now included in Office 365 P1...
Read more
"Being an MSP today is like wearing a neon sign that says, ‘Hack me! I’m the gateway to 100...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
