"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

CyberHoot Vulnerability Alert Management Process (VAMP) Rating: Critical/Red July 19th, 2022:...
Read more
CyberHoot Vulnerability Alert Management Process Rating (VAMP): Critical/Red June 15th, 2022:...
Read more
CyberHoot Vulnerability Alert Management Process Rating (VAMP): Critical/Red June 7th, 2022: CyberHoot...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Software as a Service (SaaS) applications...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity and Infrastructure...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Geofencing is a technology for setting...
Read more
February 18th, 2022: If you’re using PHP in your network, check that you’re using the latest...
Read more
Software as a Service (SaaS) applications have transformed businesses over the last decade with...
Read more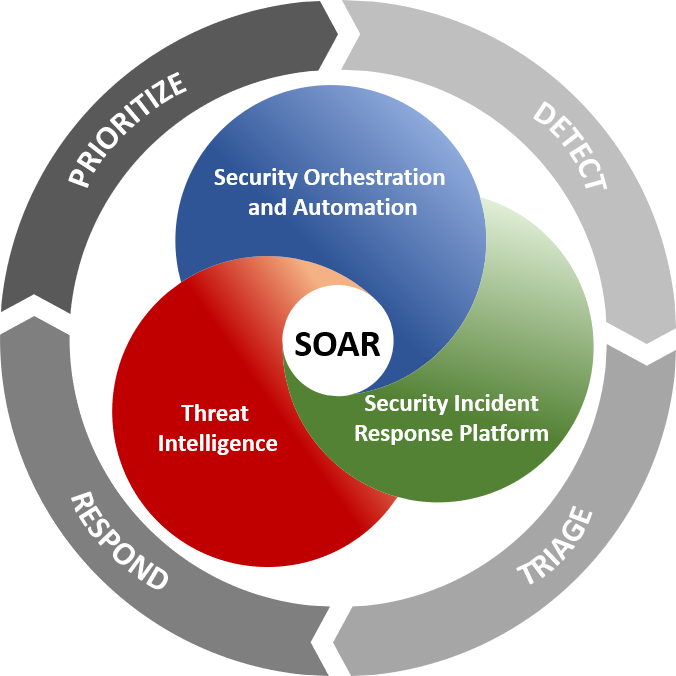
Security Orchestration, Automation, and Response (SOAR) is a stack of compatible software programs...
Read more
A new social media service, Nextdoor, is gaining steam as we come out of the COVID-19 pandemic. The...
Read more
A Transaction Lock refers to the step taken by mobile payment app users to secure their accounts...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
