"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."

Cyber Insurance is a form of insurance for businesses and individuals against Internet-based threats....
Read more
Digital Content Management (DCM) is the process for collection, delivery, retrieval, governance...
Read more
An Application Programming Interface (API) is a set of definitions and protocols for building...
Read more
The Tor Browser is a web browser designed for anonymous web browsing and protection against traffic...
Read more
Digital Rights Management (DRM) are measures taken to protect digital media copyrights. DRM tries to...
Read more
A Data Spill, or Data Leak, is the accidental or deliberate exposure of information into an...
Read more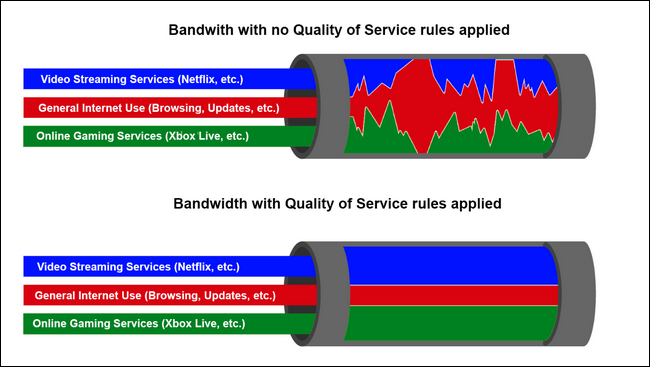
Quality of Service (QoS) is a technology that manages and prioritizes certain types of data traffic on...
Read more
Network Behavior Analysis (NBA), also known as "Behavior Monitoring" is the collection and analysis of...
Read more
A Blended Threat is a computer network attack that seeks to maximize the severity of damage and speed...
Read more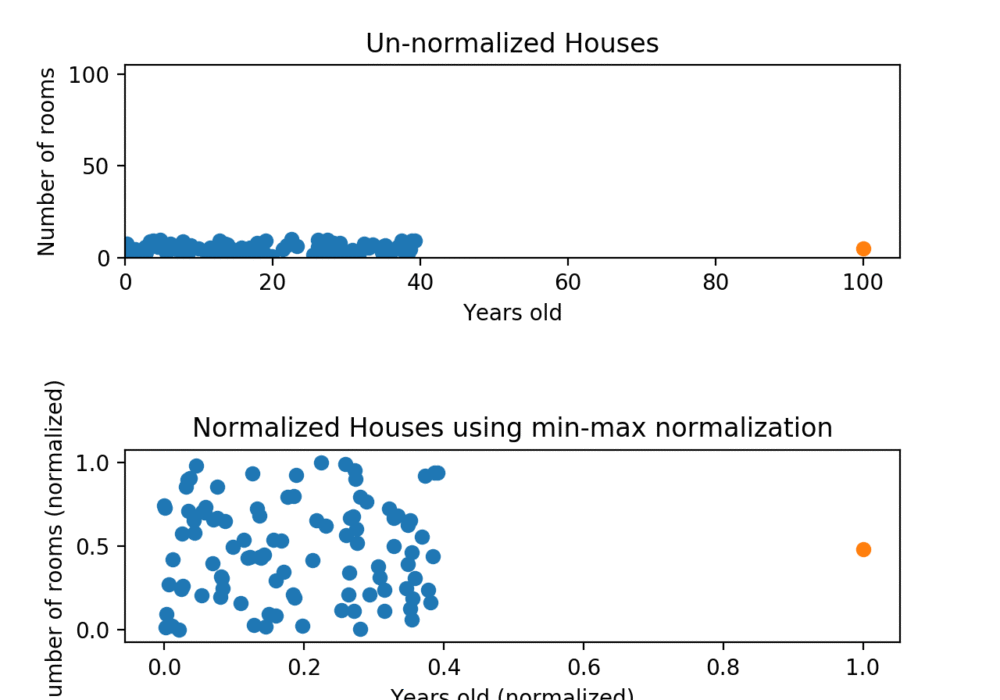
Data Normalization is a process of reorganizing information in a database to meet two...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
