"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."

Image Source A Threat Agent is an individual, group, organization, or government that conducts or...
Read more
Image Source Threat Analysis in cybersecurity work is where a person identifies and assesses the...
Read more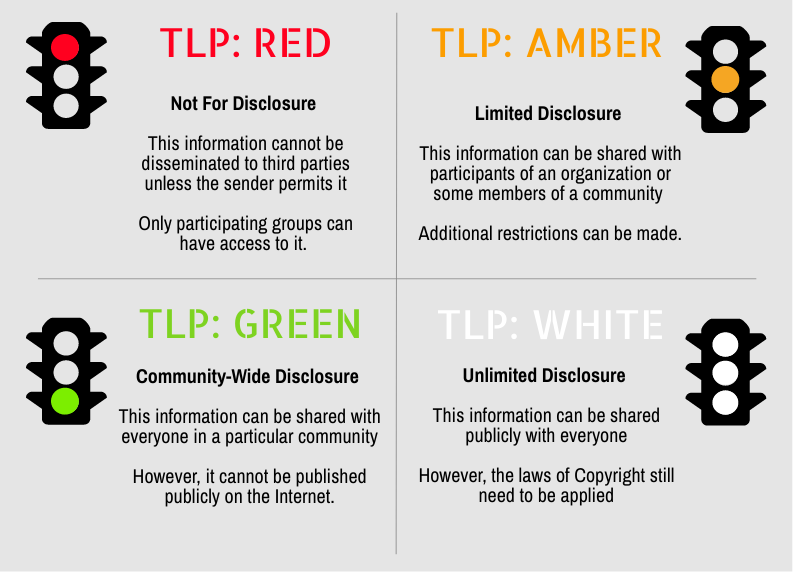
Secure your business with CyberHoot Today!!! Sign Up Now Traffic Light Protocol (TLP) is a set of...
Read more
Image Source A vulnerability is a characteristic or specific weakness that renders an organization...
Read more
An Allow list, also known as a Permit List or (deprecated: White List), is a list of...
Read more
Image Source A Work Factor is an estimate of the effort or time needed by a potential adversary, with...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
