“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
Image Source An Industrial Control System is an information system used to control industrial...
Read more
Image Source Risk Acceptance (Accept) refers to accepting the risk that is presented to you or your...
Read more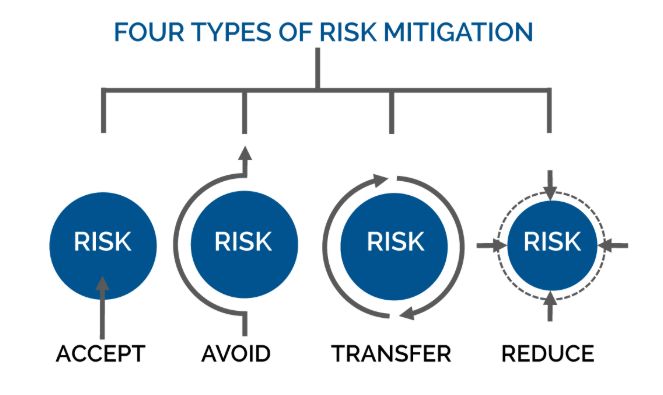
Image Source Mitigation occurs when assessing risk. When assessing risk there are many ways to work...
Read more
Image Source An investigation is a systematic and formal inquiry into a qualified threat or...
Read more
Image Source A Work Factor is an estimate of the effort or time needed by a potential adversary, with...
Read more
Image Source Tokenization is a way for credit card information (also called the Primary Account Number or...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more
Access Control Access control is a security technique that regulates who or what can view or use...
Read more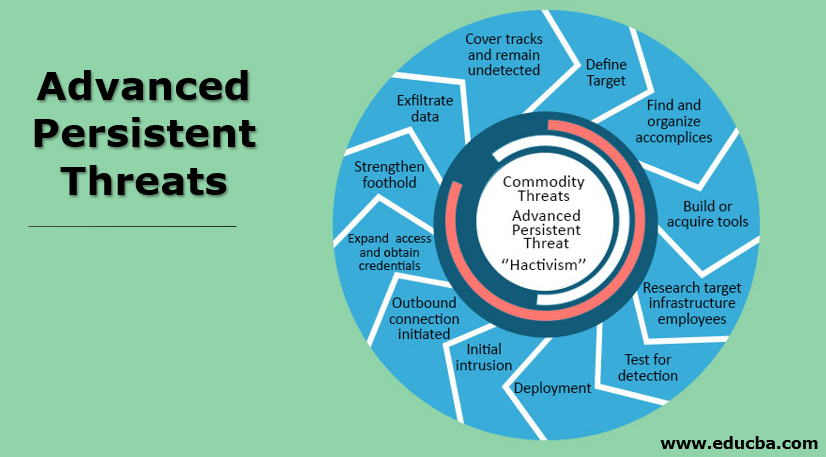
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
