"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

In April of 2021, Apple unveiled the AirTag, a tracking device that can be put on nearly anything so...
Read more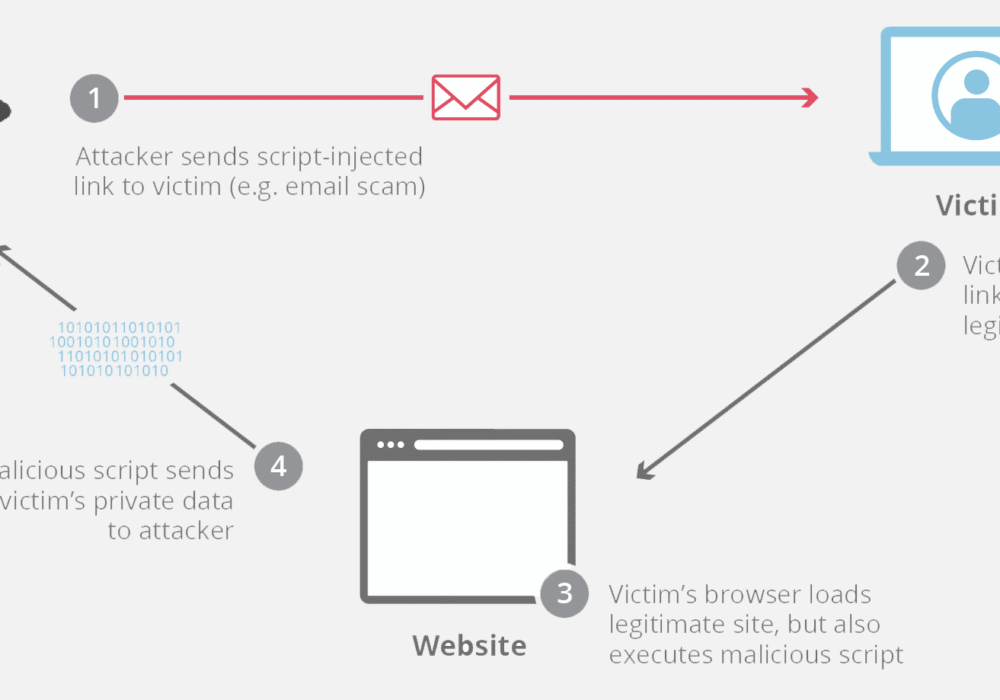
Cross-Site Scripting (XSS) is an attack vector where hackers inject malicious code into a vulnerable...
Read more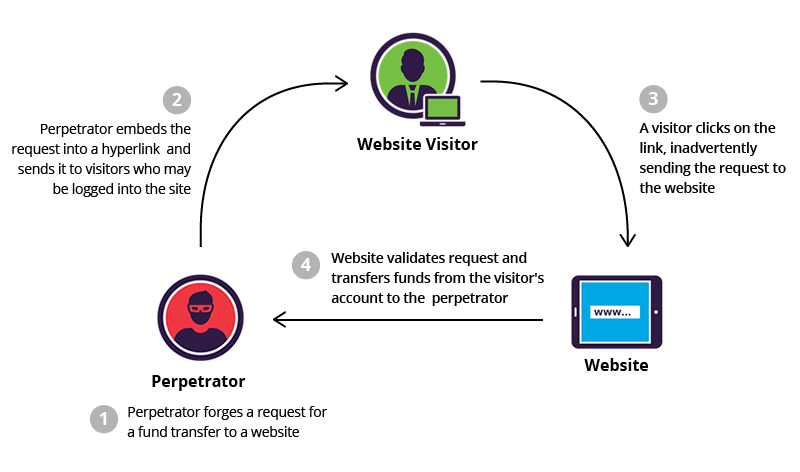
Cross-Site Request Forgery (CSRF), also known as XSRF, is an attack method that fools a web browser...
Read more
A Brute Force Attack is a strategy used by hackers trying to break into your data, password, or...
Read more
A countermeasure in the cybersecurity world, is an action, procedure, or technique that...
Read more
Cyber Criminals are individuals or teams of people who use technology to commit malicious...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious Code is harmful computer code or...
Read more
An Active Attack is a network exploit where hackers strive to change or exfiltrate data on the target's...
Read more
Image Source Antivirus Software is a program that monitors a computer or network to detect or...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
