This month we need to talk about something big. Not doomsday big, but pay-attention-now big.
On April 7th, Anthropic quietly previewed an AI model called Claude Mythos. They tested it against every major operating system and browser and it found critical vulnerabilities in all of them. The compute cost to find a 27-year-old flaw that decades of expert human audits had missed? About $50. They locked Mythos down immediately and formed a coalition called Project Glasswing, pulling in roughly 40 to 50 of the world’s largest software providers, including Microsoft, Google, Apple, Amazon, and Cisco, to patch what Mythos found before the wrong people find it first.
Here is the part that matters to you and your team.
Project Glasswing covers 40 to 50 organizations. Your business runs on hundreds of software tools built by vendors who are not in that coalition. Everyone is about to face a flood of vulnerability disclosures, shorter patching windows, and pressures they have never seen before. Some analysts are comparing this moment to Y2K, a concentrated scramble that eventually gets resolved. CyberHoot is in this camp. We can overcome this coming storm, and when we come out the other side, software will be forever changed!
The time to prepare is now, not after the first breach makes the news.
The good news is this: a trained, alert team is still the best defense you have. Patching windows must shrink while defensive scanning with advanced AI tools must start. Encourage employees to report suspicious activity (without fear), and keep sharp through regular training.
That is exactly what we are here to help you build.
This month we are covering three threats your team needs to understand right now.
In Claude Mythos Opened Pandora’s Box. Project Glasswing Is Racing to Close It, we break down what this AI watershed moment means for your organization and what practical steps to take now.
In When the “CEO” Calls and Asks You to Move Money Fast, we look at voice-based impersonation attacks that succeed because they sound real, feel urgent, and move faster than most employees are trained to question.
In When the Attack Looks Just Like You, we examine how attackers are impersonating trusted people, familiar brands, and normal business behavior to slip past suspicion entirely.
The storm may be manageable. But only if you start preparing before it arrives.
Read on.
Craig CEO, Co-Founder, CyberHoot



Liking CyberHoot? We need your help. Please leave us your review at G2.com!
– G2
For more information on how to leave a CyberHoot review, please watch the brief video overview below. Note: to avoid fraudulent reviews, each review website will require to you to create and validate your identity through an email account registration process.

Data Integrity is the assurance that information remains accurate, complete, and unaltered from its origin to its final use. It ensures that data has not been changed, corrupted, or tampered with, whether during storage, processing, or transmission. This is a core component of the CIA triad (Confidentiality, Integrity, and Availability).
Please note: CyberHoot is upgrading all Power Users to Autopilot for free. Contact support@cyberhoot.com to schedule your free upgrade. Power platform will be retired later this year Sept. 2026.
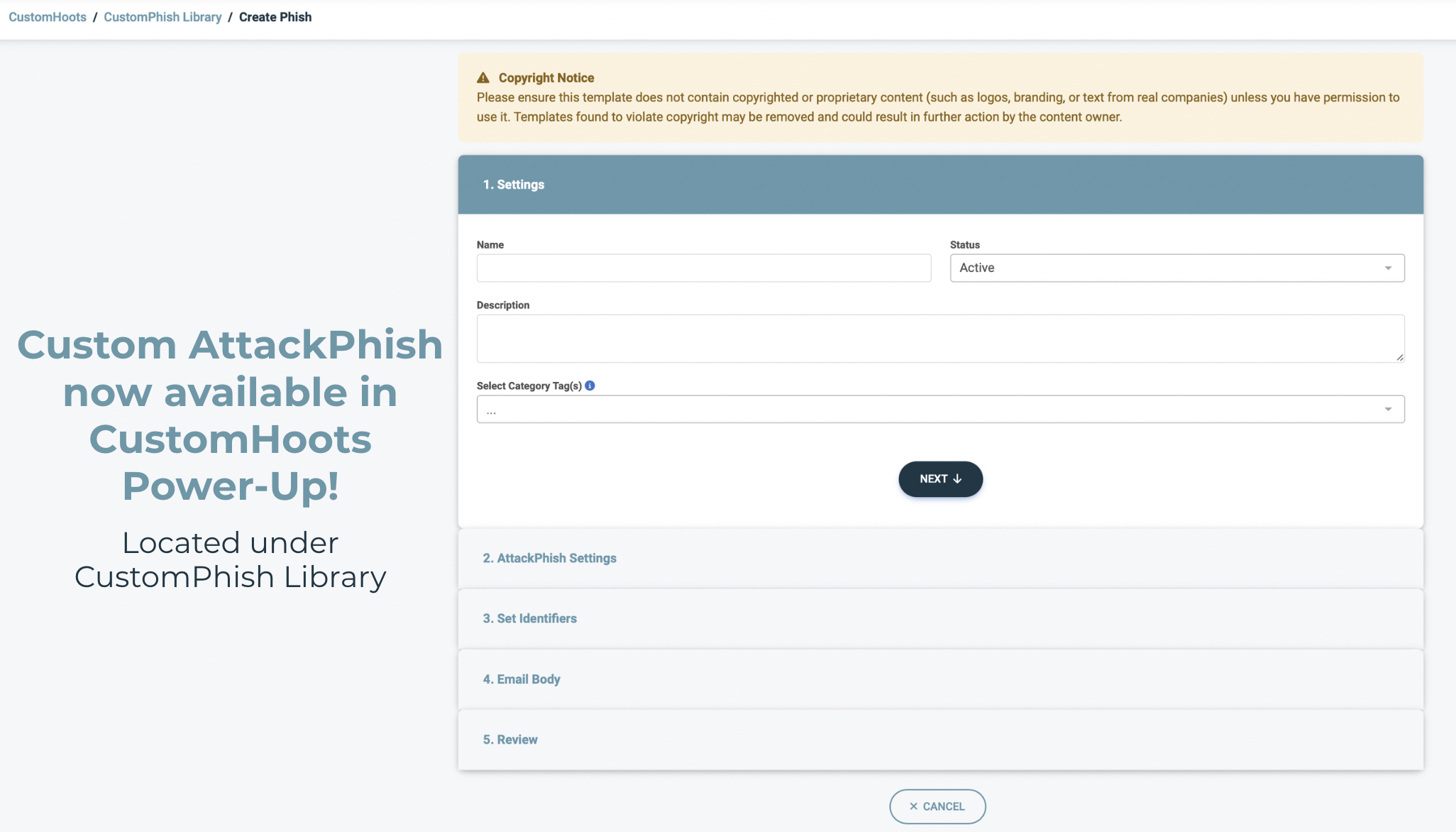
We’re excited to introduce Custom AttackPhish, a new feature within CyberHoot’s Autopilot platform that gives administrators greater flexibility when running phishing simulations. With Custom AttackPhish, (located in our CustomHoots Power-Up) admins can create and launch customized phishing campaigns that better reflect the real-world threats their users may encounter.
This helps organizations deliver more relevant security awareness training while improving users’ ability to recognize and respond to phishing attempts.
If you need additional help, you can always reach our support team at support@cyberhoot.com.

Enroll in CyberHoot’s Referral Program today and start earning a 20% share of all revenue generated for one year by those who register through your exclusive referral link. As a referral partner, not only will you receive financial rewards, but you’ll also experience the satisfaction of aiding others in becoming more security-conscious, safeguarding them against cyber threats. Don’t hesitate, sign up now at https://cyberhoot.com/referral-program/.
Referral through Autopilot’s Dashboard:
Join CyberHoot in our mission to create a more aware and better secured world! Recommend CyberHoot Autopilot to a friend, and they will enjoy a complimentary first month. For every new sign up who uses your referral link, you will receive a free month added to your account. This offer is exclusively for first-time CyberHoot registrants.
Know someone who had a close call recently with a cyber attack, phishing email, or social engineering phone call? Recommend CyberHoot’s free cybersecurity training. They’ll receive six (6) videos (each video is 3-4min.) and one of our positive reinforcement, hyper-realistic, phishing simulations. All for free.
Registration: https://cyberhoot.com/individuals
CyberHoot White Paper Download – How HootPhish Improves upon AttackPhish
All New: 2025 Infographics on Cybersecurity Statistics
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
