
Gmail’s built-in “Report Phishing” button sends reports only to Google’s internal Alert Center — it does not forward to a custom mailbox. To route user-reported phishing emails to CyberHoot, a Gmail add-on from the Google Workspace Marketplace is required.
Required add-on: Demisto Phishing Add-on
| Feature | Details |
|---|---|
| One-click reporting | Users click a single button to report suspicious email |
| Forwarding method | Forwards the original email as an attachment to your configured address |
| Admin-configurable | Destination email is set once by the admin and applies to all domain users |
| Marketplace listing | workspace.google.com/marketplace |
1️⃣ Install the Add-on (Admin Only)
1. Go to the Demisto Phishing Add-on page in the Google Workspace Marketplace:
👉 https://workspace.google.com/marketplace/app/demisto_phishing_addon/98372960675
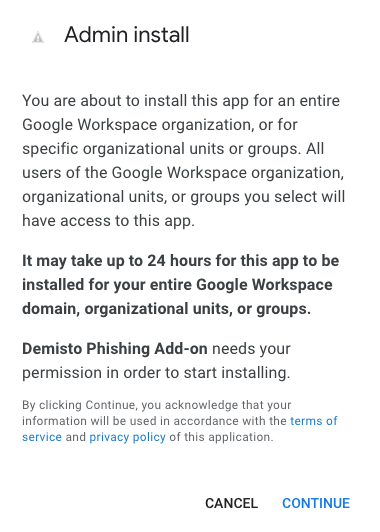
2. Click Admin Install
3. Select Everyone at your organization
4. Check the box to agree to the Terms of Service, Privacy Policy, and Google Workspace Marketplace Terms of Service
5. Click Finish
2️⃣ Configure the Add-on (Admin Only)
Once installed, the admin must configure the destination email from within Gmail. This is a one-time setup and the settings apply to all users in the domain.
1. Open Gmail while signed in as a Google Workspace admin
2. In the right sidebar, click the Demisto add-on icon to open the panel

3. The panel will display an Admin Setup section with the following fields:

| Field | What to enter |
|---|---|
| Forwarding email address | Enter reportphish@cyberhoot.com to send reports directly to CyberHoot, or enter your internal security team’s mailbox if you prefer to review reports before they are forwarded |
| Add-on display name | Enter a name your users will recognise, e.g. Report Phishing |
| Add-on logo URL | Optionally enter your own logo URL, or use CyberHoot’s logo:https://cyberhoot.com/wp-content/themes/cyberhoot-theme/images/logo.png |
📌 If you choose to use an internal mailbox as the forwarding address, make sure to configure that mailbox to forward a copy of all received reports to reportphish@cyberhoot.com so CyberHoot can process them. See Step 3 below.
3️⃣ Forward Reports to CyberHoot (If Using an Internal Mailbox)
Skip this step if you entered reportphish@cyberhoot.com directly in Step 2. If you are routing reports through an internal security mailbox first, follow these steps to forward a copy to CyberHoot.
Google Workspace blocks automatic external forwarding by default, so you must first enable it for the reporting mailbox.
3️⃣.1️⃣ Allow External Forwarding for the Reporting Mailbox
reportphish@cyberhoot.com4️⃣ Validate the Full Flow
.eml attachment📌 Result:
User-reported messages are automatically forwarded to CyberHoot with a single click, with no further action required from the user.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

OAuth tokens don't expire when employees leave, passwords change, or apps go rogue. Your security program needs...
Read more
Most breaches don't start with a hacker in a hoodie cracking code at 3am. They start with your username and a...
Read more
Article Updates: As of May 6th 2026, every major U.S. AI lab, including Google DeepMind, Microsoft, xAI,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
