User Behavior Analytics (UBA) is the tracking, collecting, and assessment of user data and activities using monitoring systems. UBA examine archived data from network and authentication logs collected and stored in log management and SIEM systems. They analyze and identify patterns of user traffic caused by known behaviors, both normal and malicious. UBA systems are primarily intended to provide cybersecurity teams with information they can use to find patterns in data sets too large for a human to manipulate. While UBA systems don’t take action based on their findings, they can be configured to automatically adjust the difficulty of authenticating users who show unusual behavior.
Behavior analysis systems first emerged in the early 2000s as tools to help marketing teams analyze and predict customer buying patterns. Today, user behavior analytics tools have more advanced profiling and exception monitoring capabilities than SIEM systems and are used for two main functions:
While UBA tools are valuable and can help improve the security of your business, it’s important to look at your budget and determine if you have room for a UBA system. UBA’s aren’t necessarily vital to a security strategy, but are great to have if you are willing to pay for them.
Sources:
Additional Reading:
5 Emerging Security Technologies Set to Level the Battlefield
Related Terms:
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
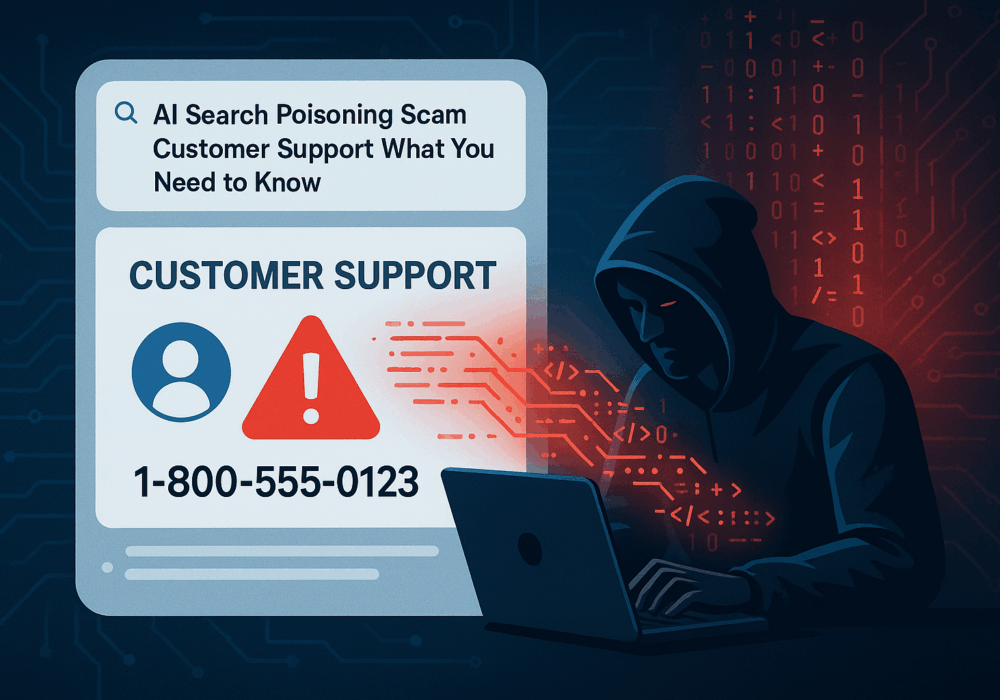
Cybercriminals always follow Internet eyeballs. Not literally, but figuratively. And today's eyeballs are...
Read more
Active Attacks on Messaging Apps The Cybersecurity and Infrastructure Security Agency (CISA) recently issued...
Read more
The world of work has changed enormously since COVID-19. Gone are the days when IT admins sat behind a corporate...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
