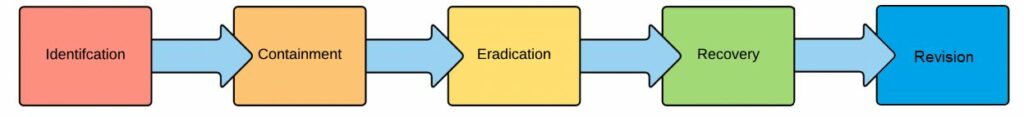
Recovery refers to phase four (4) in CyberHoot’s view of Cybersecurity Incident Handling. In this phase, incident handlers proceed with activities that seek to restore essential services and operations in the short and medium term and fully restore all capabilities in the longer term.
Phase 1 is Identification of an incident in progress through confirmation activities.
Phase 2 is Containment: containing the incident.
Phase 3 is Eradication: Eliminating the infection, malware, or hackers from your environment.
Phase 5 is Revision: once the dust clears from an incident, you should always go back to identify opportunities for improvement. These are revisions to your security program.
Related Terms: Incident Response, Identification, Containment, Eradication, Revision
Source: NIPP
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

OAuth tokens don't expire when employees leave, passwords change, or apps go rogue. Your security program needs...
Read more
Most breaches don't start with a hacker in a hoodie cracking code at 3am. They start with your username and a...
Read more
Article Updates: As of May 6th 2026, every major U.S. AI lab, including Google DeepMind, Microsoft, xAI,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
