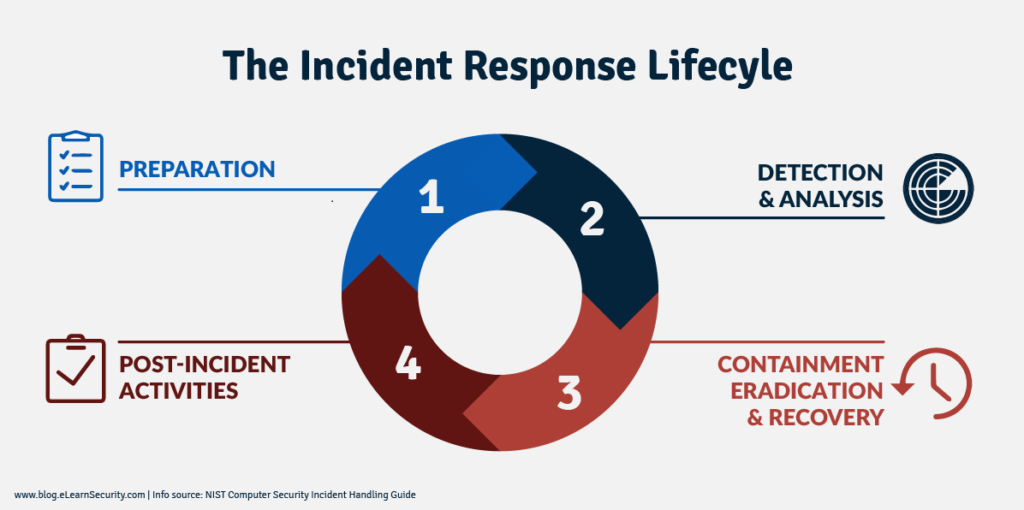
Containment refers to the limiting and preventing of further damage to a computer system or network. Containment is a part of incident response, right before the eradication of the threat. Examples of containing a cyber security incident include: Blocking and logging of unauthorized access, blocking malware sources, closing specific ports and servers, changing administrator passwords, relocating website home pages, and isolating systems or networks.
Your business needs to take proactive measures today to first reduce its chances of being hit by ransomware, phishing, or other cybersecurity attacks. Secondly, validate backups and disaster recovery plans are current and functioning in case you end up hit with ransomware. CyberHoot recommends the following best practices to avoid, prepare for, and prevent damage from these attacks:
Start building your robust, defense-in-depth cybersecurity plan at CyberHoot.
Related Terms: Eradication, Recovery, Revision
Source: Bluegrass Cyber Security
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
