A Buffer Overflow Attack happens when a program tries to fill a block of memory (a memory buffer) with more data than a buffer is supposed to hold. Buffers are essentially the areas of storage that temporarily hold data while it is being transferred from one location to another.
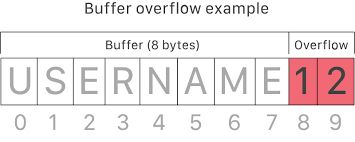
When a hacker sends malicious inputs to a vulnerable application, they can force the application to execute malicious code to take control of the machine or crash the system. Buffer overflow vulnerabilities are known to be caused by programmer mistakes that are easy to understand but much harder to avoid and protect against.
Attackers exploit buffer overflow issues by overwriting the memory of an application, changing the execution path of the program, triggering a response that damages files or exposes sensitive information. For example, an attacker may introduce extra code, sending new instructions to the application to gain privileged access to your IT system.
Source: NetSparker, Imperva
Additional Reading:
Related Terms:
Buffer overflow prevention pertains first and foremost to businesses developing software. Train developers on the OWASP top 10 mistakes in coding to help them understand the importance of boundary checks and input validation in the code they write. Most static code scanning solutions on the market test for input validation and will alert you if you do not have this set right. Always build static and dynamic code scanning into your software development lifecycle.
For non-development businesses, you need to pay attention to vulnerabilities that may be disclosed in the COTS software you purchase and use at your business. Sometimes they will have buffer overflow vulnerabilities which can lead to compromise of your computing systems. Always monitor your vendors security advisories and apply patches in a timely fashion to ensure your software environment is safe and secure from these and many other vulnerabilities.
Buffer overflow attacks are easily preventable whether in other peoples code or your own. Pay attention to this and avoid a costly mistake.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read more
Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read more
Not surprising when Trouble Ensues Last summer, the interim head of a major U.S. cybersecurity agency uploaded...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
