"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."

Clear Text (or plaintext) is data that is stored or transmitted without any form of encryption or obfuscation. In...
Read more
Privileged Access Management (PAM) is a cybersecurity framework and set of tools designed to secure, manage, and...
Read more
Identity Management (IDM) is the framework of policies, processes, and technologies used to ensure the right...
Read more
End-to-End Encryption (E2EE) is a method of securing digital communications so that only the sender and the...
Read more
Operational Disruption is any unexpected event, failure, or interruption that prevents normal business processes,...
Read more
Microsegmentation is a security technique that divides a network into smaller, isolated zones down to the...
Read more
A brushing scam is a deceptive tactic where online sellers or scammers send unsolicited packages...
Read more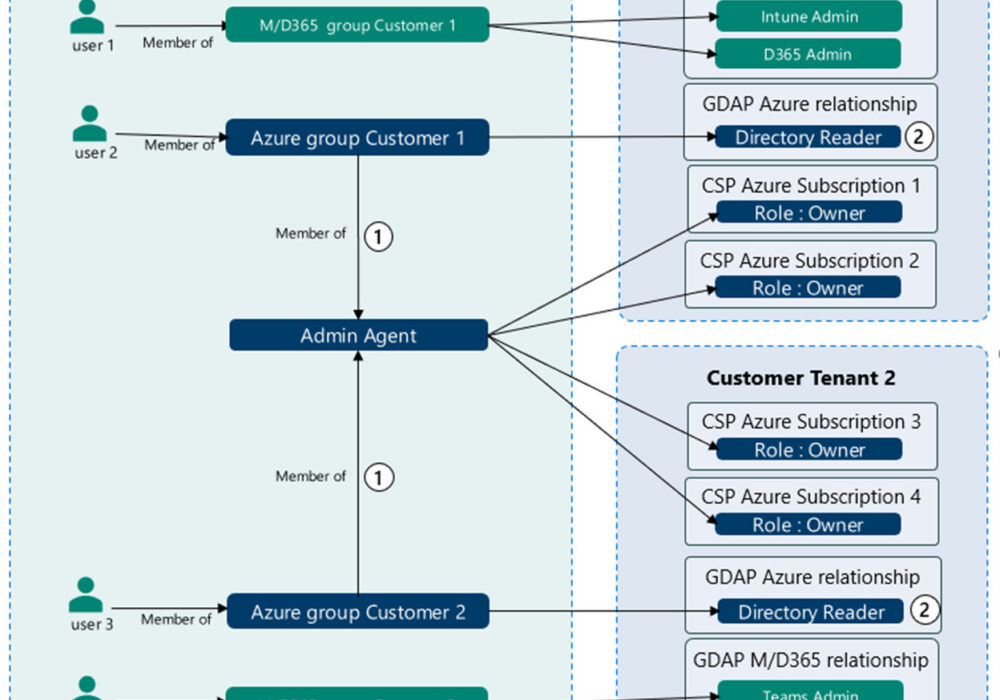
Microsoft's Granular Delegated Admin Privileges (GDAP) is a way of assigning specific...
Read more
Advertising Clean Room An "advertising clean room", also referred to as a Data Clean Room (DCR), is a term used...
Read more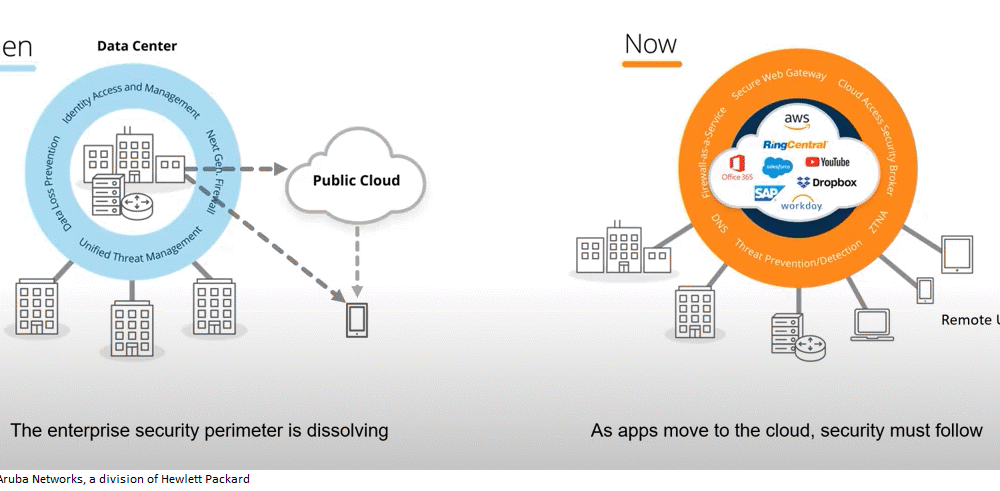
SASE Secure Access Service Edge (Pronounced: Sassy) SASE is a term coined by Gartner in 2019 to describe an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
