"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
Piggybacking is a form of cyber attack where a hacker(s) gain access to an unauthorized network,...
Read more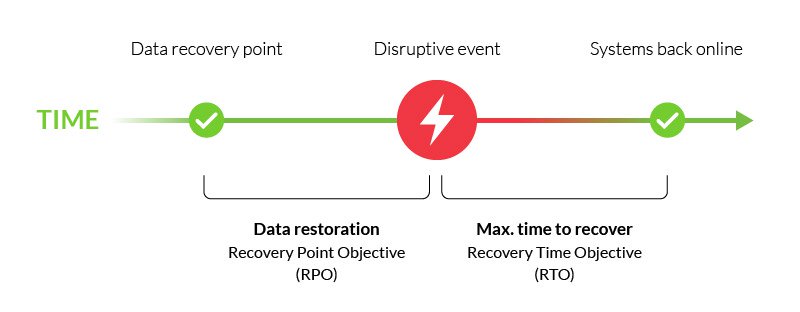
A Recovery Point Objective (RPO) is the maximum amount of data that your company is willing to...
Read more
A Recovery Time Objective (RTO) is a metric used to measure how fast you can recover your IT...
Read more
The term Restore, also known as Recovery, is the process of retrieving production data from a backup...
Read more
Eavesdropping in the cybersecurity world refers to the interception of communication between two...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
