“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”

Apple’s tracking-optional iOS 14.5 update provides privacy-preserving features, giving users the...
Read more
Fake IRS Tax Forms This week, AbnormalSecurity reported an attack on an estimated 15-50 thousand email...
Read more
The Internal Revenue Service (IRS) announced this week that in January 2021 taxpayers can apply for an...
Read more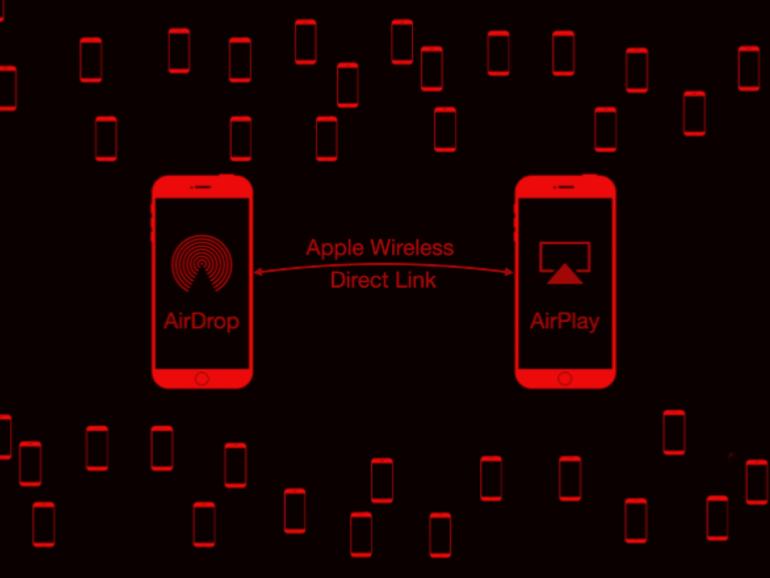
Google's Project Zero cybersecurity researcher (and white-hat hacker) Ian Beer published an article in...
Read more
For those that don't know, the webpage you're reading this article on features the security protocol of...
Read more
COVID-19 continues to force companies to deliver their services remotely. A growing threat perhaps...
Read more
The pyramids in Egypt and the Great Wall of China were built to last forever. Computer hardware and...
Read more
Work environments are evolving, presenting new opportunities for cybercriminals to compromise company...
Read more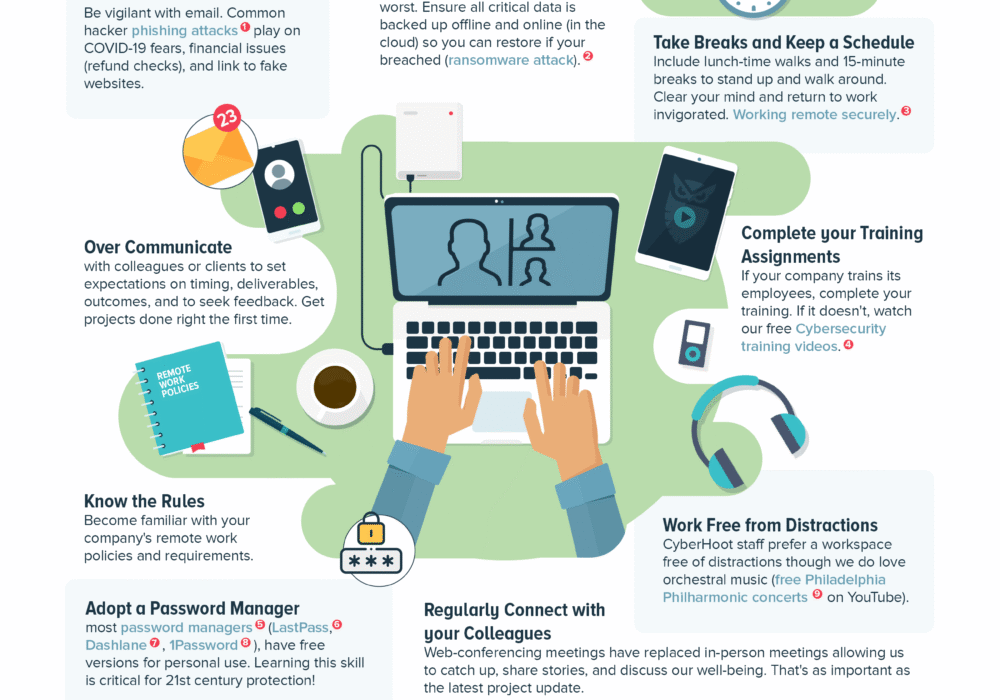
The 2020 Coronavirus pandemic has lead many workers to work from home to slow its spread. Business owners have...
Read more
Cyberwarfare is the use of sophisticated cyber weapons (viruses, worms, trojans, etc.) by one...
Read more
Facial Recognition software gets better by the day, with machine-learning and artificial...
Read more
MORE SOPHISTICATED AND DAMAGING Ransomware Attacks are Coming Belarus law enforcement officials have...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
