"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
Secure your business with CyberHoot Today!!! Sign Up Now Quantum Computing is an area of computing...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Moore’s Law is a 1965 observation made by...
Read more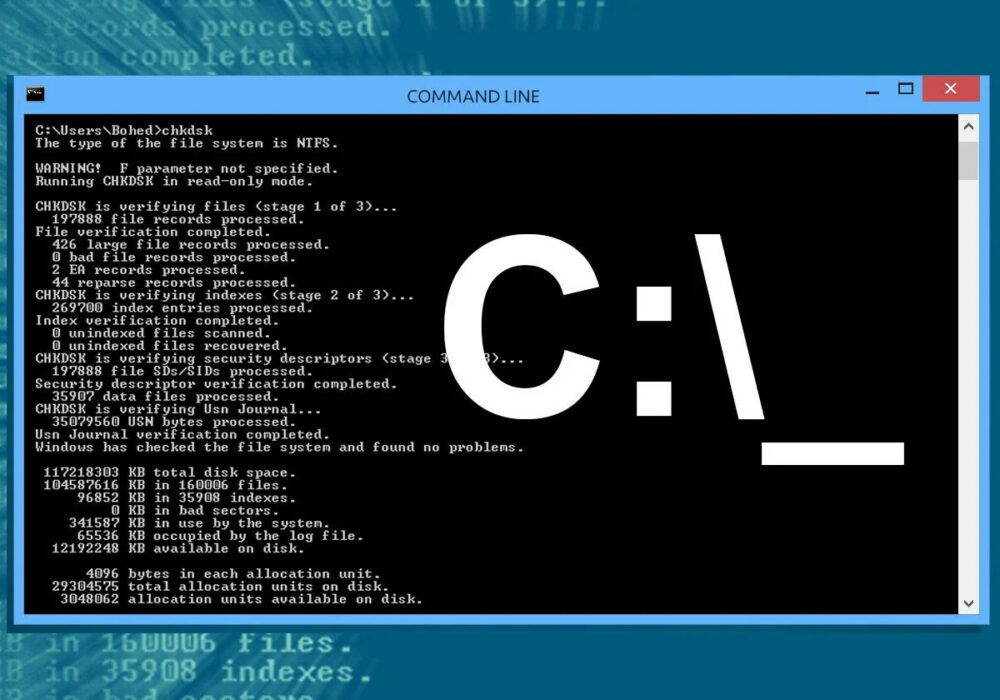
Secure your business with CyberHoot Today!!! Sign Up Now A Command Line Interface (CLI) is a...
Read more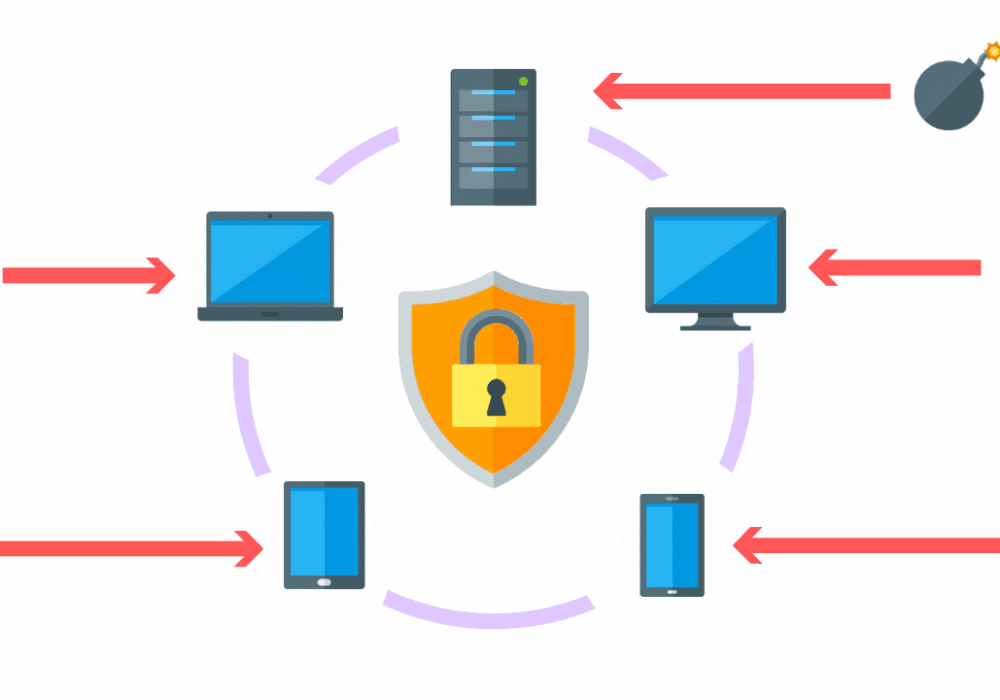
Secure your business with CyberHoot Today!!! Sign Up Now Endpoint Detection and Response (EDR), also...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Health Insurance Portability and...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Controlled Unclassified Information (CUI) is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity Maturity Model...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Purple Team is a group of cybersecurity...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Network Access Control (NAC) is the act of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now AES Encryption, also known as Advanced...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Wiper Malware is malicious software that...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Fingerprints used in cryptography are short...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
