"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

Image Source A malicious applet is a small application program that is automatically downloaded and...
Read more
Image Source Malicious Logic is hardware, firmware, or software that is intentionally included or...
Read more
Symmetric Cryptography is a branch of cryptography in which a cryptographic system or algorithms use...
Read more
A Symmetric Key is a cryptographic key that is used to perform both the cryptographic operation and...
Read more
Image Source System Integrity is the attribute of an information system when it performs its...
Read more
Image Source Tailored Trustworthy Space refers to a cyberspace environment that provides a user with...
Read more
Image Source A Threat Agent is an individual, group, organization, or government that conducts or...
Read more
Image Source Threat Analysis in cybersecurity work is where a person identifies and assesses the...
Read more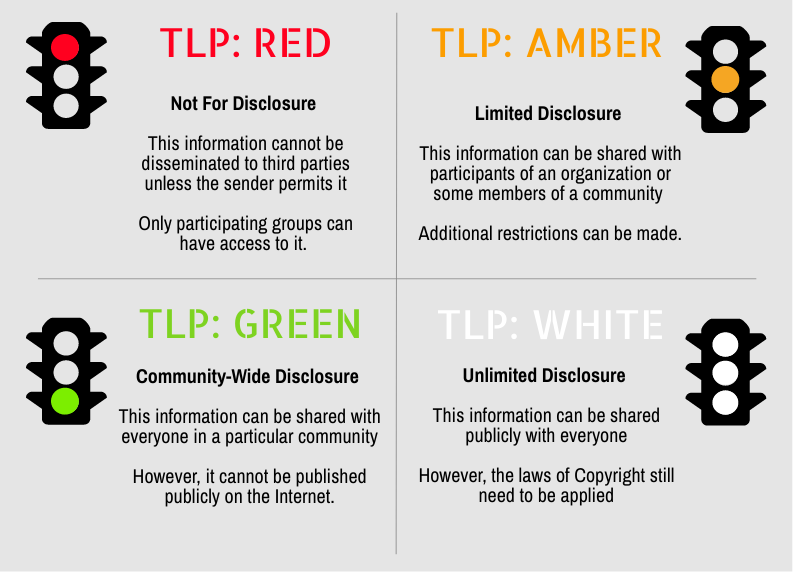
Secure your business with CyberHoot Today!!! Sign Up Now Traffic Light Protocol (TLP) is a set of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
