"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."

Image Source Risk Analysis is the systematic examination of the components and characteristics of...
Read more
Image Source A Risk Assessment is the product or process which collects information and assigns...
Read more
Image Source Risk Management is the process of identifying, analyzing, assessing, and...
Read more
Image Source Risk-Based Data Management is a structured approach to managing risks to data and information...
Read more
Image Source A Private Key is a cryptographic key that must be kept confidential and is used to...
Read more
Image Source A Secret Key is a cryptographic key that is used for both encryption and decryption, enabling...
Read more
Image Source A Public Key is a cryptographic key that may be widely published and is used to enable the...
Read more
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
Image Source Security Automation refers to the use of information technology in place of manual...
Read more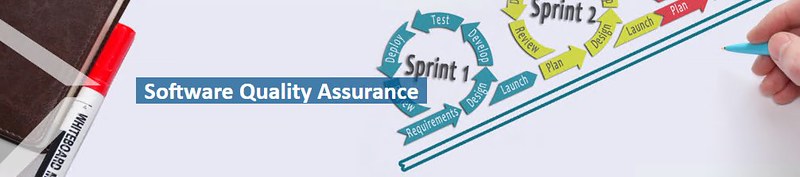
Image Source Software Assurance is the level of confidence that software is free from vulnerabilities,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
