"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."

Combining public and private keys to electronically sign messages. A Digital Signature is a value computed...
Read more
Image Source Ciphertext is data or information in its encrypted form. Ciphertext is the output when an...
Read more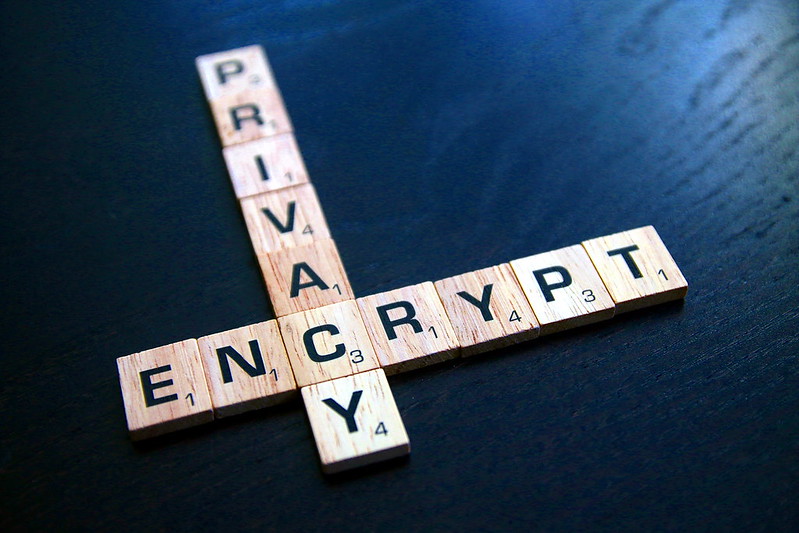
Encryption is the process of transforming plaintext into ciphertext. This is done by converting data...
Read more
Cryptography is the use of mathematical techniques to provide security services, such as...
Read more
Image Source Penetration Testing is an evaluation methodology whereby ethical hackers search for...
Read more
Image Source Incident Response is the activities that address the short-term, direct effects of an incident...
Read more
Image Source Redundancy refers to additional or alternative systems, sub-systems, assets, or processes that...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
