"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."

Image Source Interoperability is the ability of two or more systems or components to exchange information...
Read more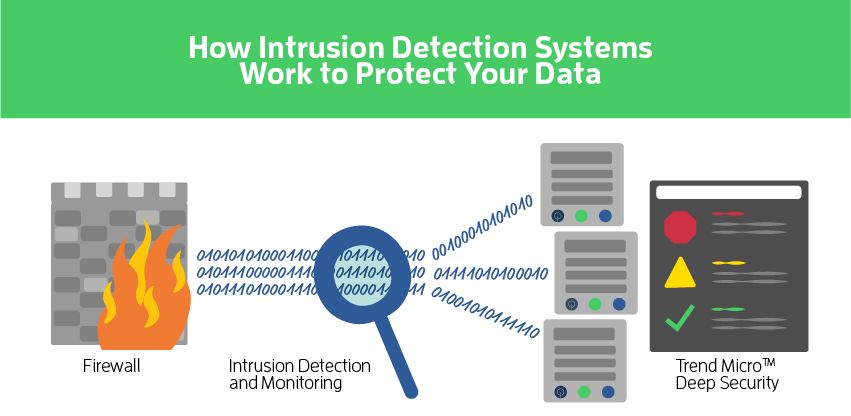
Network-based Intrusion Prevention Services (aka NIPS) is a preemptive approach to network security used to...
Read more
Image Source Intrusion Detection is the process and methods for analyzing information from...
Read more
Image Source Information Technology (IT) is any equipment or interconnected system or subsystem of equipment...
Read more
Image Source Information and Communication(s) Technology (ICT) is any information technology,...
Read more
Image Source Machine Learning and Evolution is a field concerned with designing and developing artificial...
Read more
Image Source A Moving Target Defense (MTD) is the presentation of a dynamic attack surface,...
Read more
Image Source Network Services in cybersecurity work is where a person installs, configures, tests,...
Read more
Image Source Network Resilience is the ability of a network to: (1) provide continuous operation (i.e.,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
