"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."

Decryption is the process of transforming ciphertext into its original plaintext. This is done...
Read more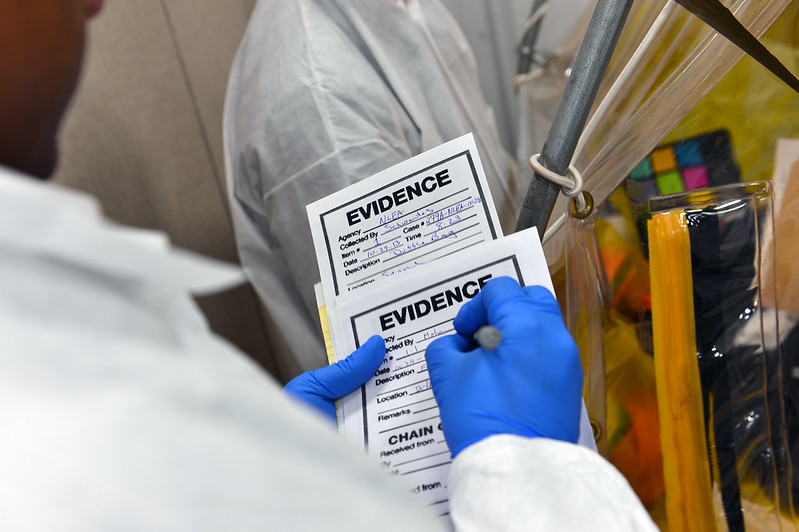
Image Source Digital Forensics is the processes and specialized techniques for gathering, retaining, and...
Read more
Cyber Criminals are individuals or teams of people who use technology to commit malicious...
Read more
Image Source In the NICE Workforce Framework, Education and Training in cybersecurity work is where a person...
Read more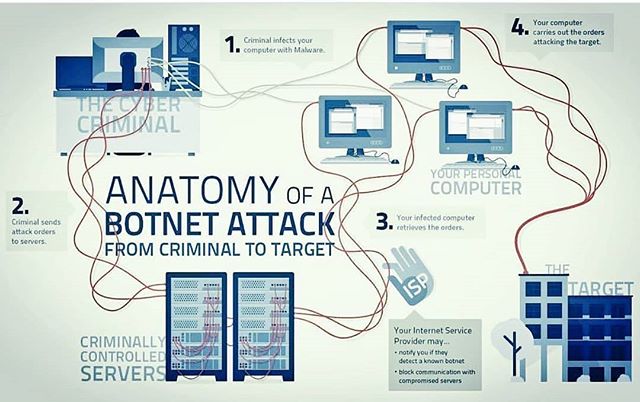
Bot(s) A Bot is a computer connected to the Internet that has been surreptitiously / secretly...
Read more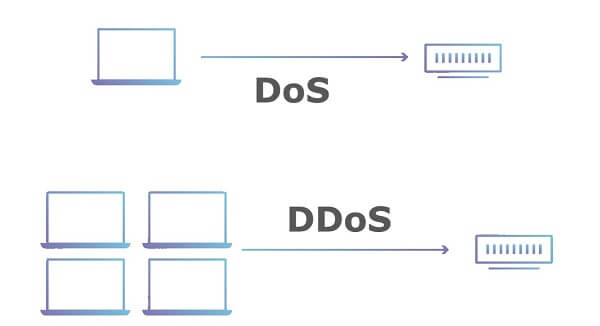
Denial of Service (DoS) is an attack that prevents or impairs the authorized use of information...
Read more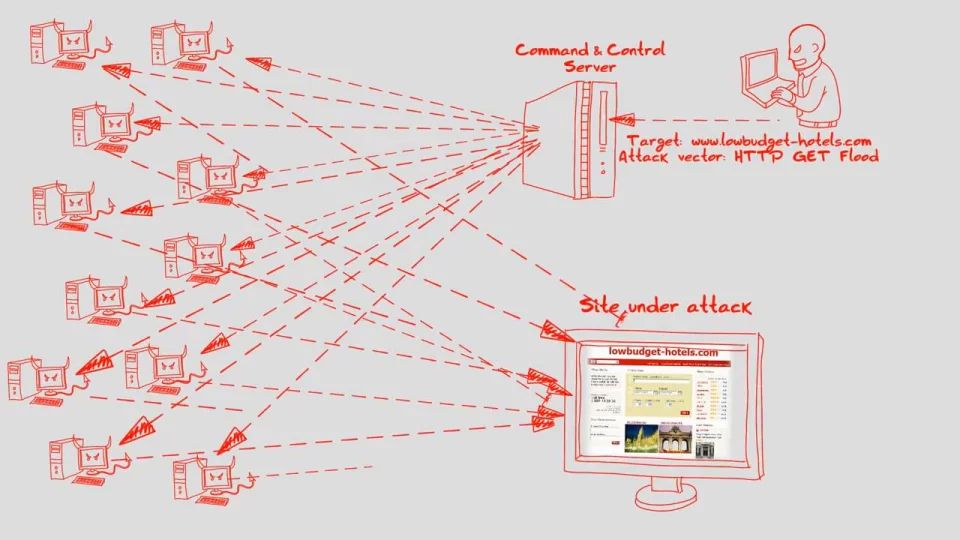
Distributed Denial of Service (DDoS) attacks are a type of Denial of Service (DoS) attacks. A...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
