"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."
Image Source A Data Breach is the unauthorized movement or disclosure of sensitive information to a party,...
Read more
Image Source Exfiltration is the unauthorized transfer of information from an information system. The types...
Read more
Image Source Data Loss Prevention is a set of procedures and mechanisms to stop sensitive data from leaving...
Read more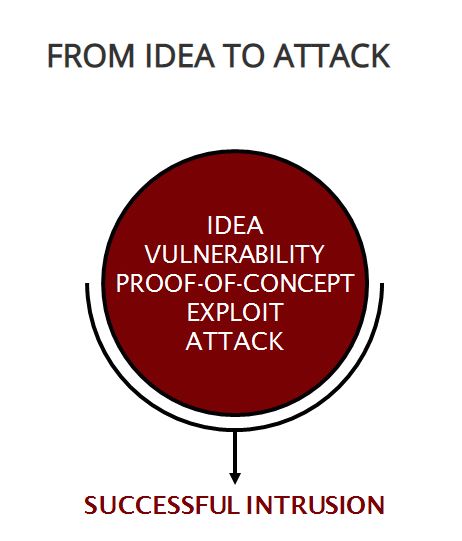
Image Source Exploitation Analysis is cybersecurity work where a person: analyzes collected...
Read more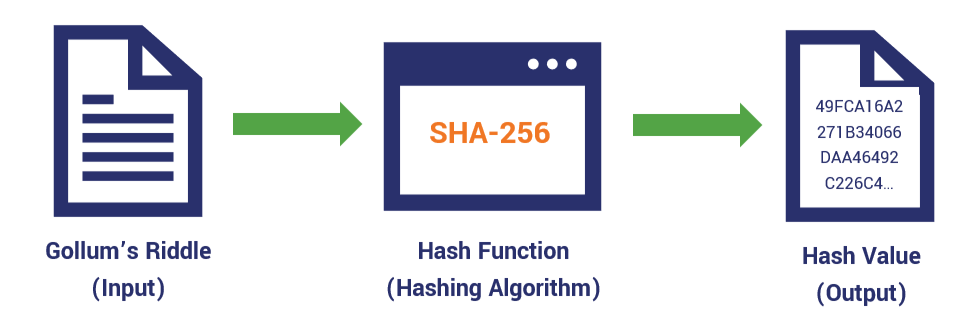
A Hash Value is a numeric value resulting from a mathematical algorithm applied to a set of data...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
