"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."

The news headlines seem to be filled with ransomware attacks of late. Business owners are taking note...
Read more
NSO, the Israeli technology company has been working with governments around the world by selling them...
Read more
Microsoft's released an Out-Of-Band (OOB) emergency patch, affecting windows systems' print-spooler...
Read more
A new social media service, Nextdoor, is gaining steam as we come out of the COVID-19 pandemic. The...
Read more
Update and Correction - 3:30pm 7/3/21: CyberHoot has confirmed from Kaseya and other cybersecurity news...
Read more
Cash is King, for now. The use of electronic payment applications has been steadily growing, according...
Read more
Lawmakers on Capitol Hill are scrambling to introduce legislation addressing overwhelming spikes in...
Read more
In May of 2021, the United States’ largest pipeline, Colonial Pipeline, halted operations due to...
Read more
[Update on JBS Ransomware attack: June 10, 2021 CyberHoot learned that backups and a strong disaster...
Read more
The FBI released a statement in April 2021, warning of cybercriminals using fake job listings to target...
Read more
A phrase that has been making waves in the financial world is Decentralized Finance (aka: DeFi). DeFi...
Read more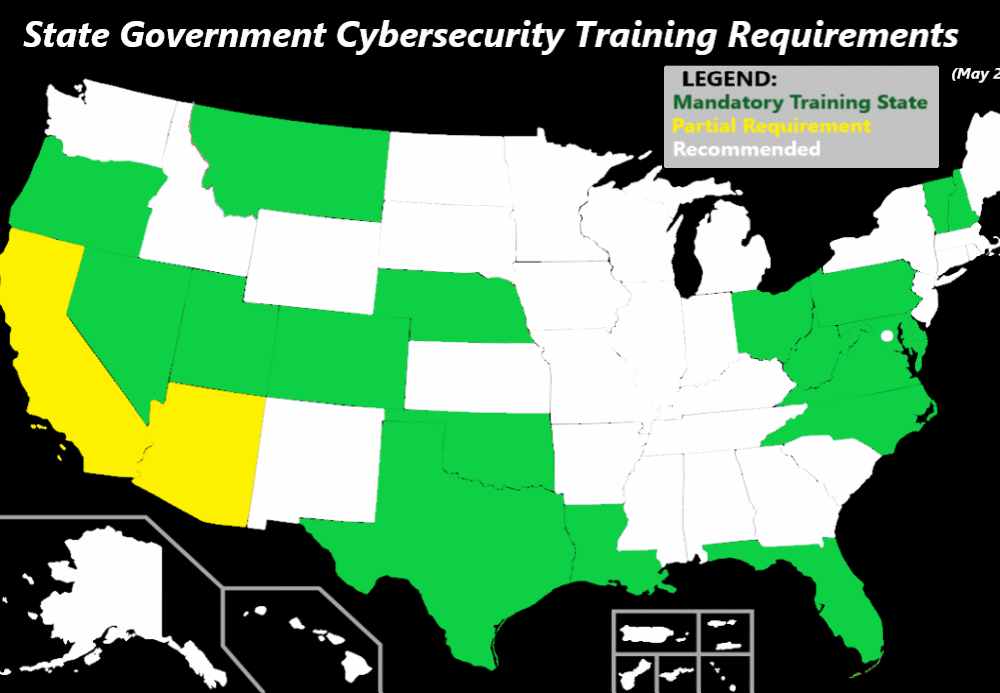
May 17, 2021: Following the Ransomware Attack on the Colonial Pipeline, Texas Governor Greg Abbott took...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
