"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”

Image Source A Moving Target Defense (MTD) is the presentation of a dynamic attack surface,...
Read more
Image Source Network Services in cybersecurity work is where a person installs, configures, tests,...
Read more
Image Source Network Resilience is the ability of a network to: (1) provide continuous operation (i.e.,...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Electronic Signature, also known as an...
Read more
Image Source Authenticity is a property achieved through cryptographic methods of being genuine and being...
Read more
Image Source Non-Repudiation is a property achieved through cryptographic methods to protect...
Read more
Image Source Operate & Maintain refers to activities providing the support, administration, and...
Read more
Image Source Operations Technology is the programmable systems or devices that interact with...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious Code is harmful computer code or...
Read more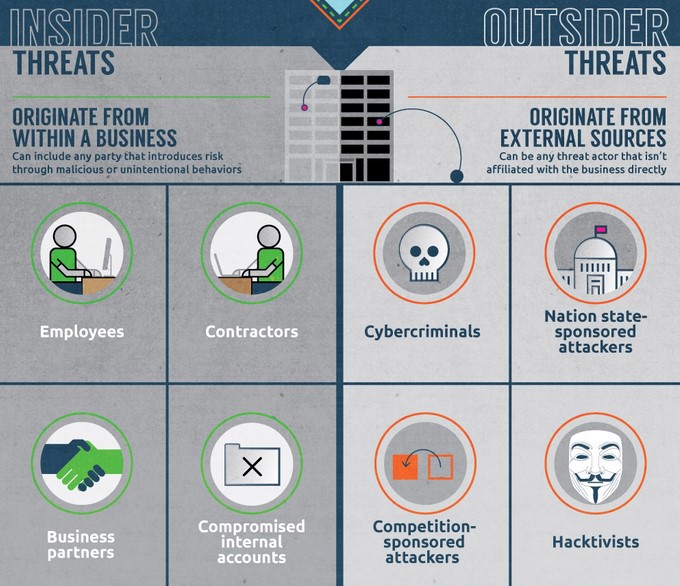
An Insider Threat is a person or group of persons within an organization who pose a potential risk of...
Read more
Image Source An Outsider Threat is a person or group of persons external to an organization who are not...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
