"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."

Authentication is the process of verifying the identity or other attributes of an...
Read more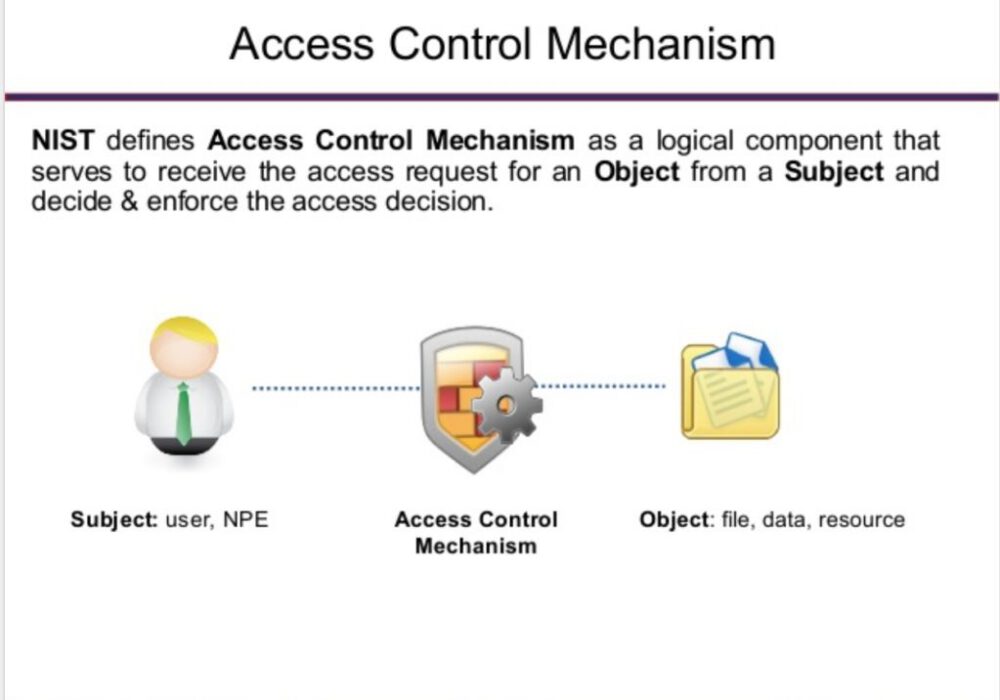
Image Source An access control mechanism is a security safeguard (i.e., hardware and software...
Read more
A Block List or Deny List, (deprecated: Blacklist), is a list of entities that are blocked or...
Read more
Image Source Active content is software that is able to automatically carry out or trigger actions without...
Read more
Decryption is the process of transforming ciphertext into its original plaintext. This is done...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
