"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
COVID-19 continues to force companies to deliver their services remotely. A growing threat perhaps...
Read more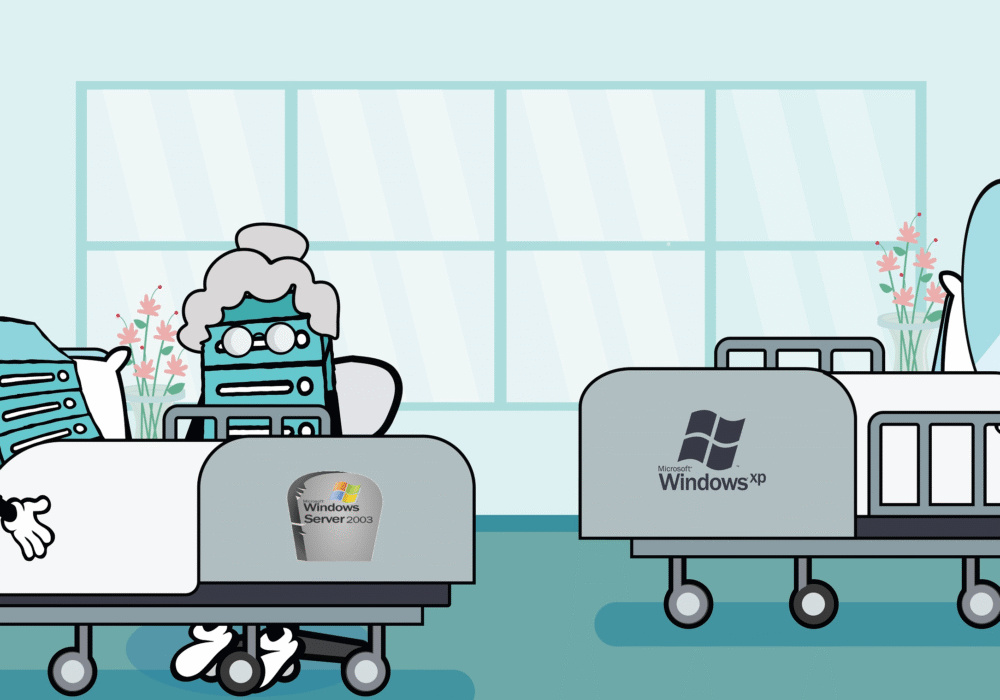
The pyramids in Egypt and the Great Wall of China were built to last forever. Computer hardware and...
Read more
Work environments are evolving, presenting new opportunities for cybercriminals to compromise company...
Read more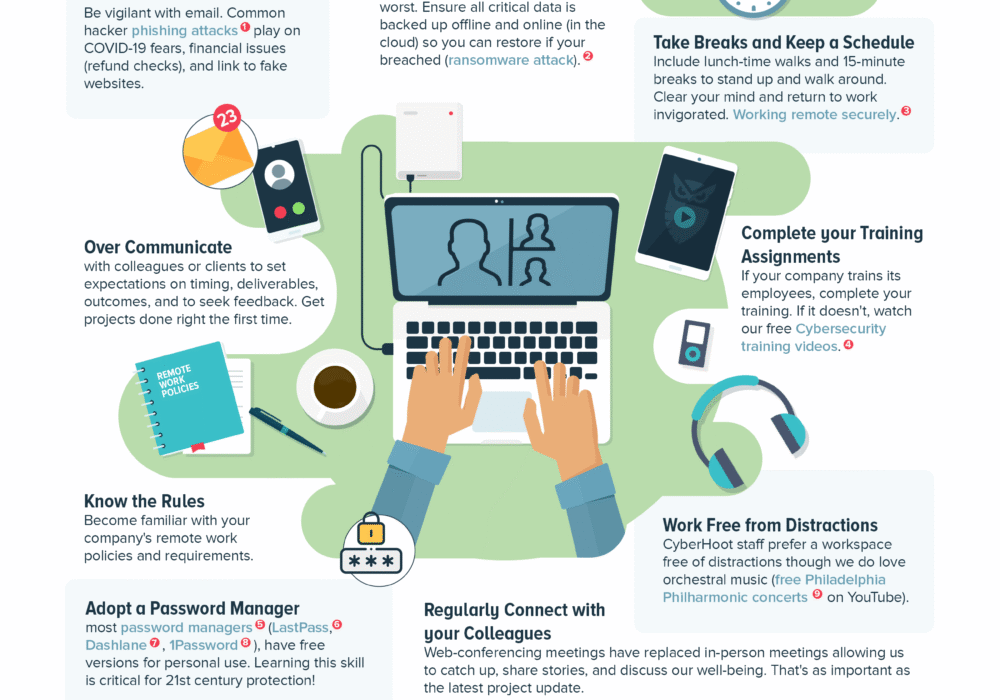
The 2020 Coronavirus pandemic has lead many workers to work from home to slow its spread. Business owners have...
Read more
There seems to be a news report every day about the latest security breach. Securing the privacy of...
Read more
Cyber Insurance is a developing market with businesses regularly purchasing cyber coverage in...
Read more
A PDF (Portable Document Format) is a file format designed to present documents consistently across...
Read more
Cyber Insurance is a developing market with businesses regularly purchasing cyber coverage in addition...
Read more
CyberHoot's Chief Information Security Officer constantly monitors the cybersecurity threats MSPs and...
Read more
A Malicious URL is a link created with the purpose of promoting scams, attacks, and fraud. By clicking...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
