"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."

Apple’s tracking-optional iOS 14.5 update provides privacy-preserving features, giving users the...
Read more
Click the image below to visit the referral registration page CyberHoot’s Press Releases are...
Read more
For people searching for love online, it has become a little difficult due to scammers' hell-bent on...
Read more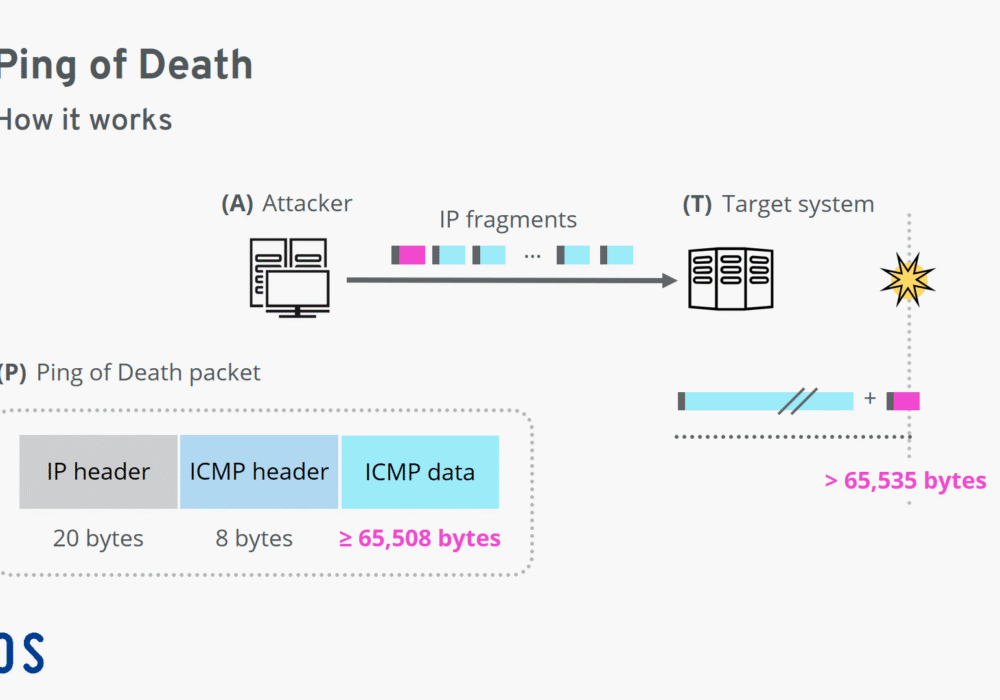
A Ping of Death (PoD) is a type of Denial of Service (DoS) attack that deliberately sends IP packets...
Read more
Click on the image below and select the 'learn more' links to take you to the HowTo tutorials. Here are...
Read more
Clearview AI has created one of the broadest and most powerful facial recognition databases in the...
Read more
Synthetic Transaction Monitoring (STM), also known as Synthetic Monitoring, is a web monitoring tool...
Read more
Common Vulnerabilities and Exposures (CVE) is a list of computer security flaws ranked on critical...
Read more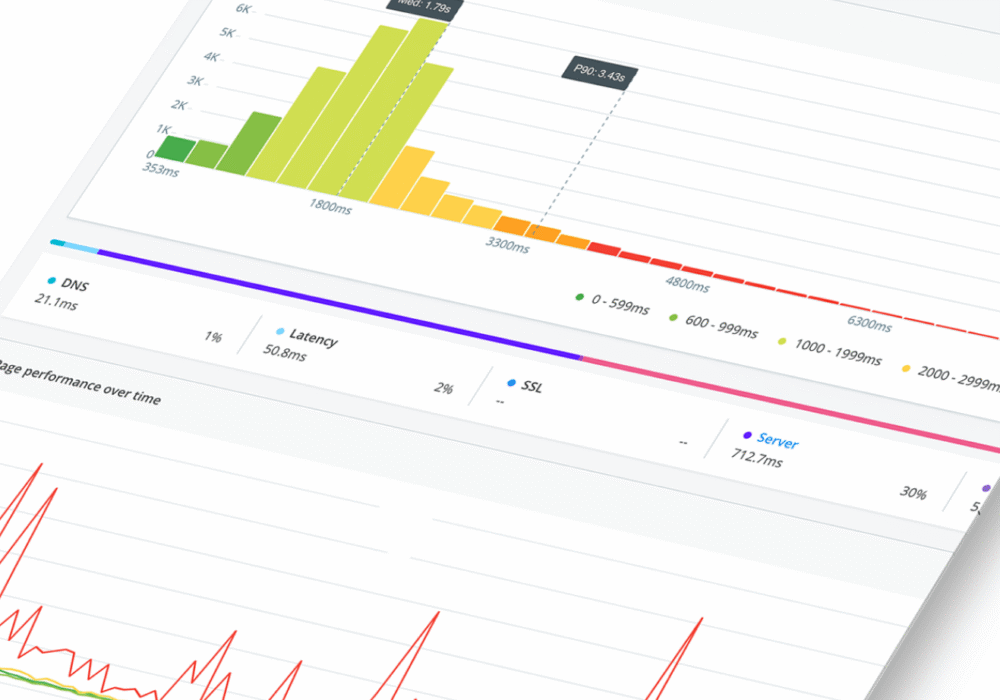
Real User Monitoring (RUM) is a form of performance monitoring that captures and analyzes user activity...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
