"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
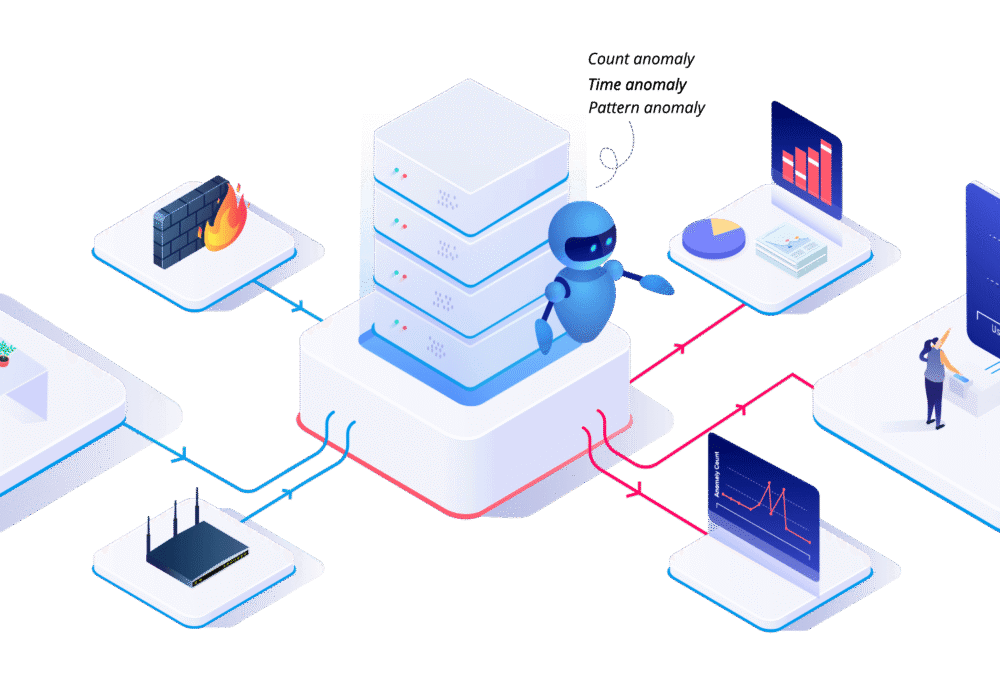
User Behavior Analytics (UBA) is the tracking, collecting, and assessment of user data and activities...
Read more
Steganography is the interesting but potentially dangerous technique of hiding data or malware code...
Read more
Blockchain is a digital record of transactions. The name comes from its structure where specific...
Read more
The popular musician Grimes sold some animations she made with her brother Mac on a website called 'Nifty...
Read more
Non-Fungible Tokens (NFTs) are unique, easily verifiable digital assets that can represent...
Read more
Oct.1st, 2020: The US Treasury Department's Office of Foreign Assets Control (OFAC) warned...
Read more
Jailbreaking is the exploiting of manufacturer or carrier operating systems, often by removing...
Read more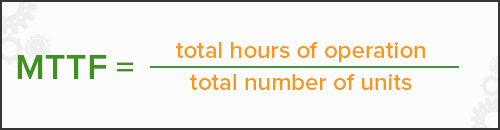
Mean Time to Failure (MTTF) and sometimes references as Mean Time For Failure (MTFF) is the length of...
Read more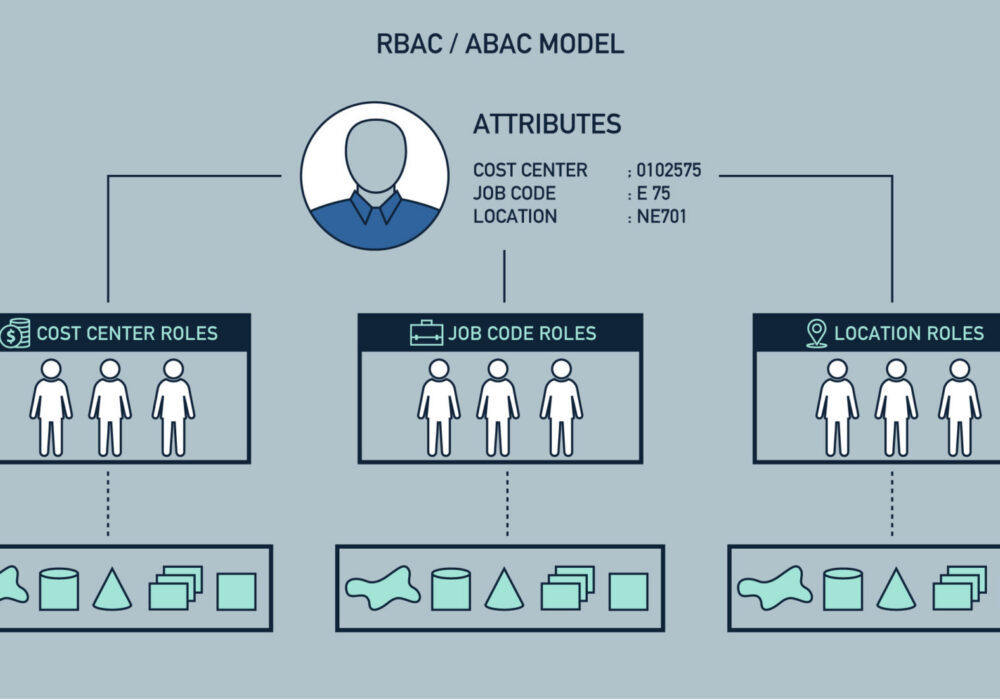
Role-Based Access Control (RBAC) is a strategy of limiting network access based on the roles of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
