"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”

[Update on JBS Ransomware attack: June 10, 2021 CyberHoot learned that backups and a strong disaster...
Read moreOverview CyberHoot provides the ability to optionally assign policies, videos, and programs to your users....
Read more
The FBI released a statement in April 2021, warning of cybercriminals using fake job listings to target...
Read more
Business Email Compromise (BEC) is when an email account, often in a company's finance department, is...
Read more
A phrase that has been making waves in the financial world is Decentralized Finance (aka: DeFi). DeFi...
Read more
Click the image below to view a larger version CyberHoot For MSPs <- Click Here CMIT MSP...
Read more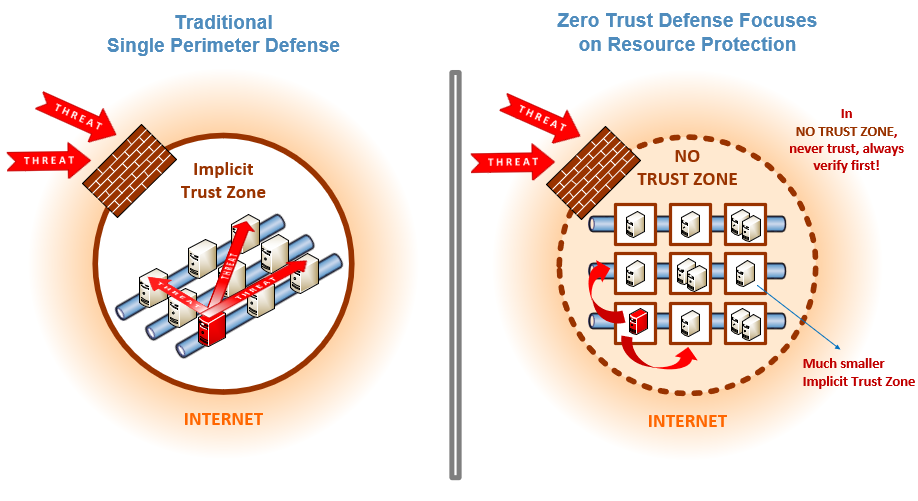
Zero Trust is a security strategy focused on the belief that organizations shouldn't automatically...
Read more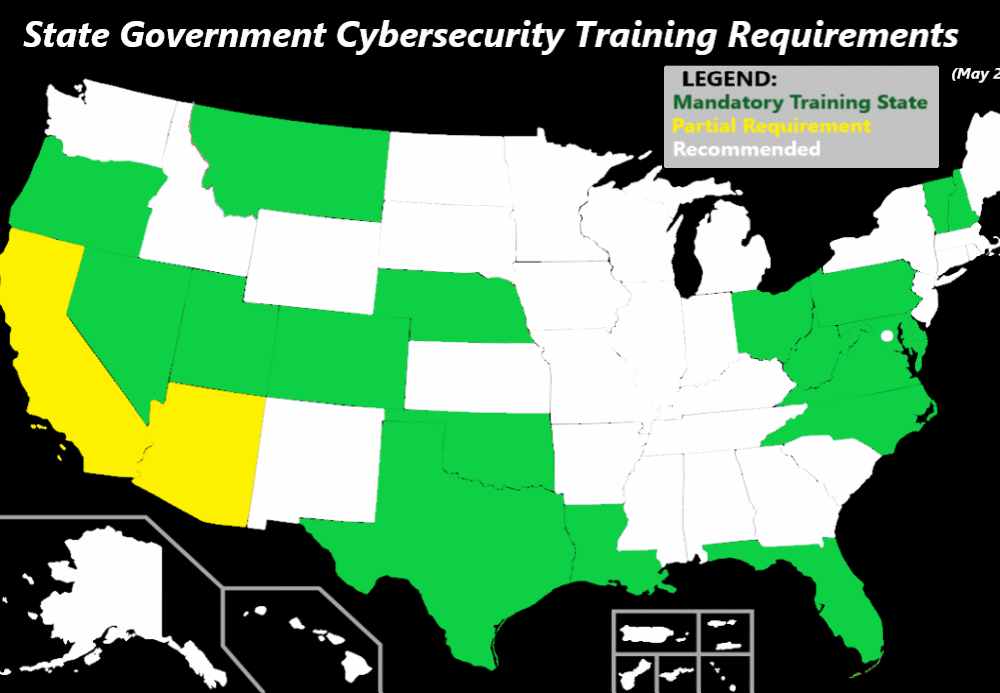
May 17, 2021: Following the Ransomware Attack on the Colonial Pipeline, Texas Governor Greg Abbott took...
Read more
The Ransomware Task Force (RTF) is a group of high-profile security vendors who teamed up with the...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
