"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."

Image Source Operate & Maintain refers to activities providing the support, administration, and...
Read more
Image Source Operations Technology is the programmable systems or devices that interact with...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious Code is harmful computer code or...
Read more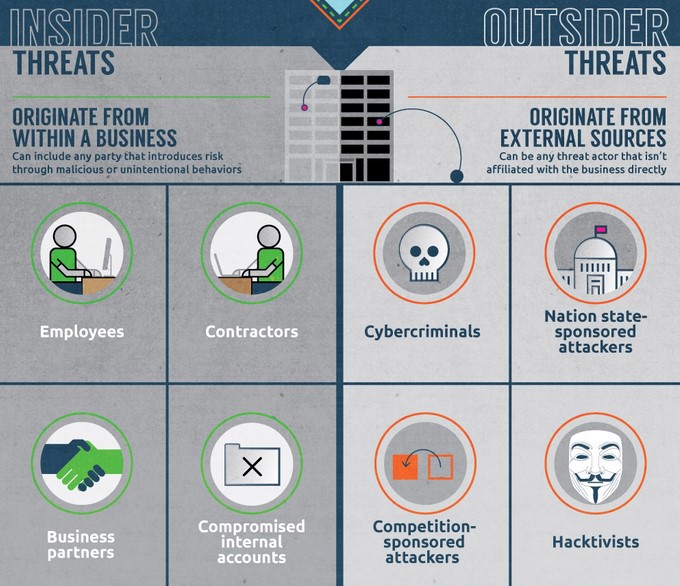
An Insider Threat is a person or group of persons within an organization who pose a potential risk of...
Read more
Image Source An Outsider Threat is a person or group of persons external to an organization who are not...
Read more
Image Source Oversight & Development is a category consisting of specialty areas providing leadership,...
Read more
An Active Attack is a network exploit where hackers strive to change or exfiltrate data on the target's...
Read more
Image Source A Passive Attack is an actual assault perpetrated by an intentional threat source that attempts...
Read more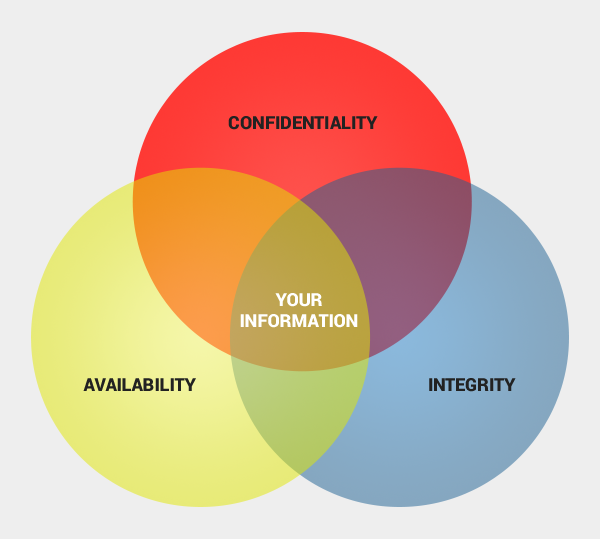
Availability is the property of being accessible and usable upon demand, where in cyber security...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
