"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
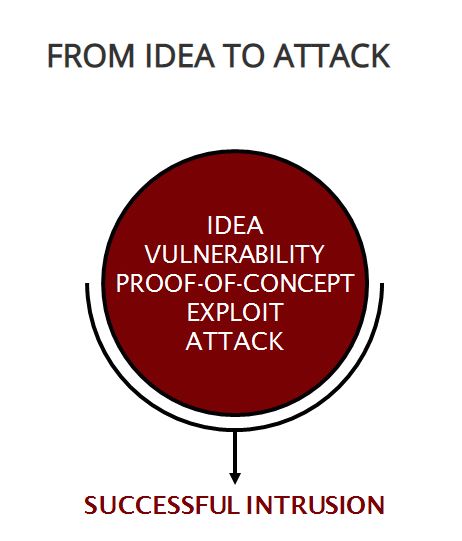
Image Source Exploitation Analysis is cybersecurity work where a person: analyzes collected...
Read more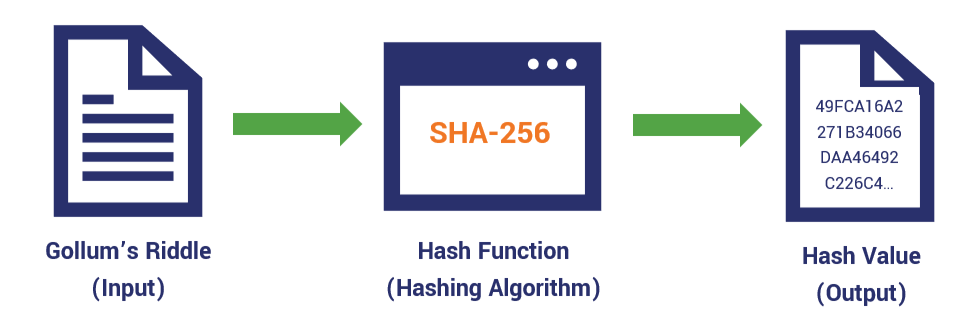
A Hash Value is a numeric value resulting from a mathematical algorithm applied to a set of data...
Read more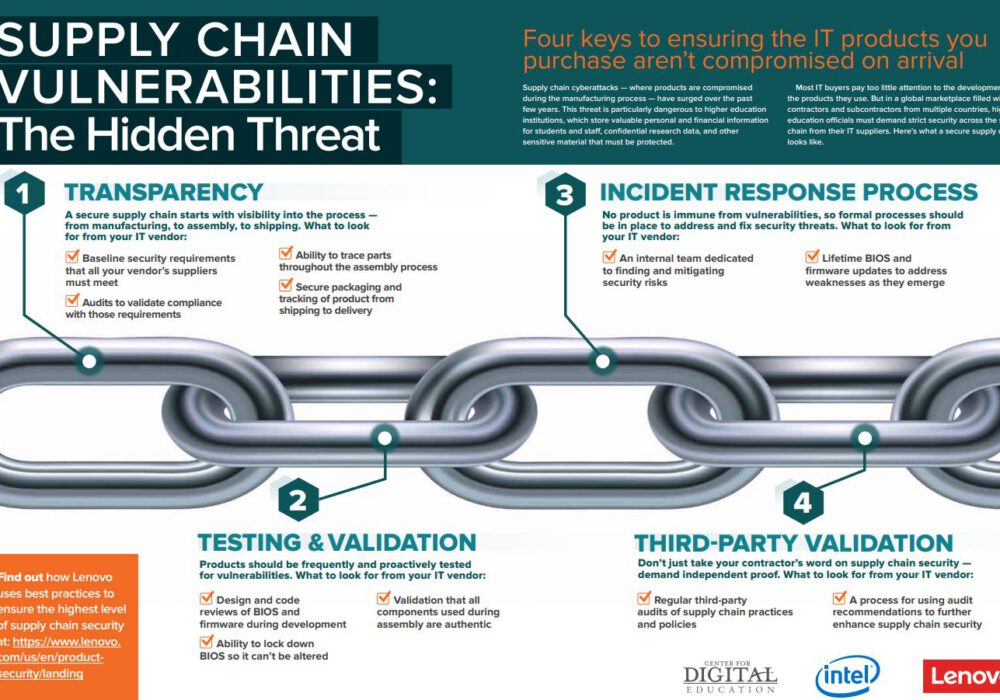
Image Source An Supply Chain Threat is a man-made threat achieved through exploitation of the information...
Read more
Identity and Access Management (IAM) are the methods and processes used to manage subjects and their...
Read more
Image Source Cybersecurity is the activity or process, ability or capability, or state whereby information...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
