"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."

A PDF (Portable Document Format) is a file format designed to present documents consistently across...
Read more
Cyber Insurance is a developing market with businesses regularly purchasing cyber coverage in addition...
Read more
CyberHoot's Chief Information Security Officer constantly monitors the cybersecurity threats MSPs and...
Read more
A Malicious URL is a link created with the purpose of promoting scams, attacks, and fraud. By clicking...
Read more
SSAE Compliance, also known as Statement on Standards for Attestation Engagements and Compliance, is a...
Read more
All-Source Analysis is the analysis of threat information from multiple sources, disciplines, and...
Read more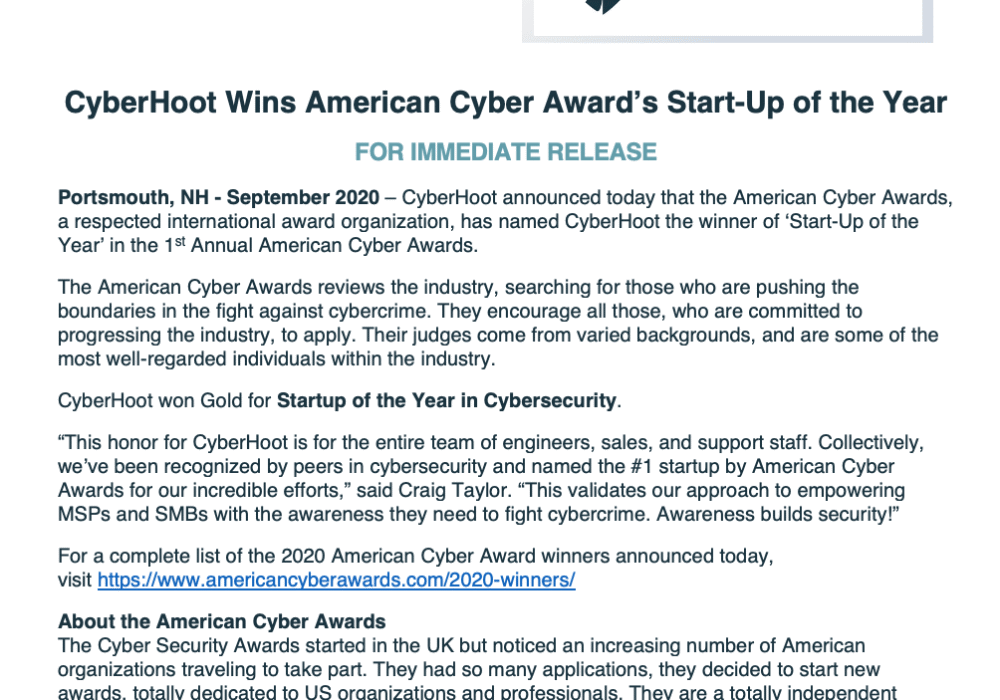
Click To View Larger Version CyberHoot’s Press Releases are published on a monthly basis. To see the...
Read more
Cybersecurity firm BlueVoyant published a report on August 27, 2020, finding that State and Local...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
