"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."

Data Sanitization is the process of permanently and irreversibly destroying data on a storage device in...
Read more
Deep Learning is a type of Machine Learning and Artificial Intelligence (AI) that mimics the way...
Read more
Artificial Intelligence (AI) refers to human-like intelligence presented by a computer, robot, or other...
Read more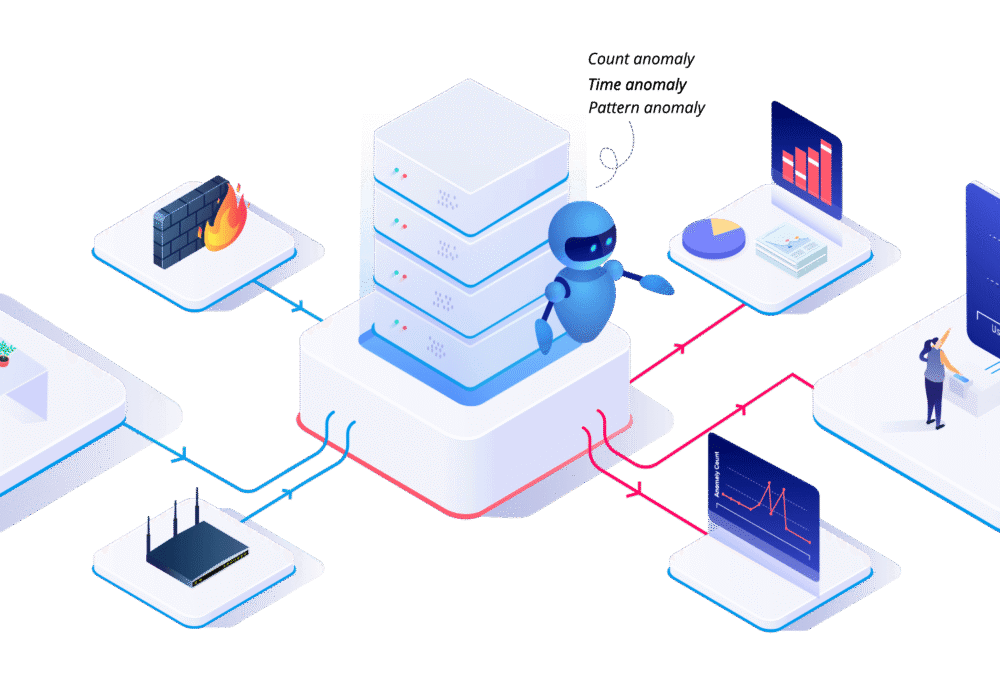
User Behavior Analytics (UBA) is the tracking, collecting, and assessment of user data and activities...
Read more
Steganography is the interesting but potentially dangerous technique of hiding data or malware code...
Read more
Blockchain is a digital record of transactions. The name comes from its structure where specific...
Read more
The popular musician Grimes sold some animations she made with her brother Mac on a website called 'Nifty...
Read more
Non-Fungible Tokens (NFTs) are unique, easily verifiable digital assets that can represent...
Read more
Oct.1st, 2020: The US Treasury Department's Office of Foreign Assets Control (OFAC) warned...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
