"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

Secure your business with CyberHoot Today!!! Sign Up Now Error Detection in cybersecurity refers to...
Read more
January 7th, 2022: CyberHoot has investigated a new form of malware known as Malsmoke. This malware is...
Read more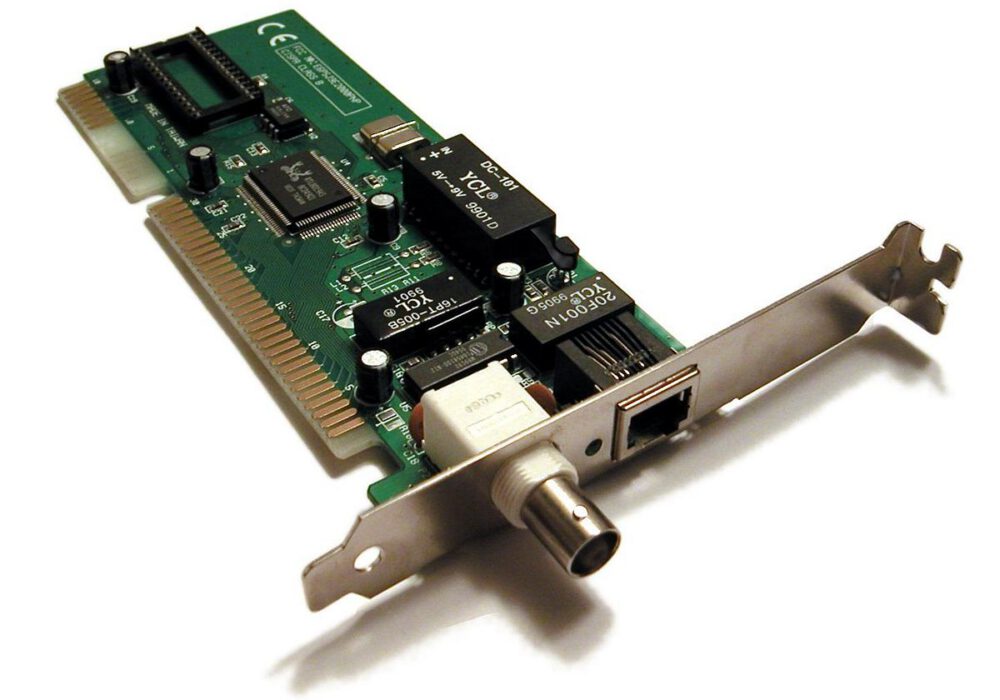
Secure your business with CyberHoot Today!!! Sign Up Now A Network Interface Card (NIC) provides...
Read more
As a Managed Service Provider (MSP), you know your customers are serious about defending against...
Read more
The Open Systems Interconnection (OSI) Model is a conceptual model created by the International...
Read more
Layer 2 Networks refers to the second layer of the Open Systems Interconnection (OSI) Model, which is...
Read more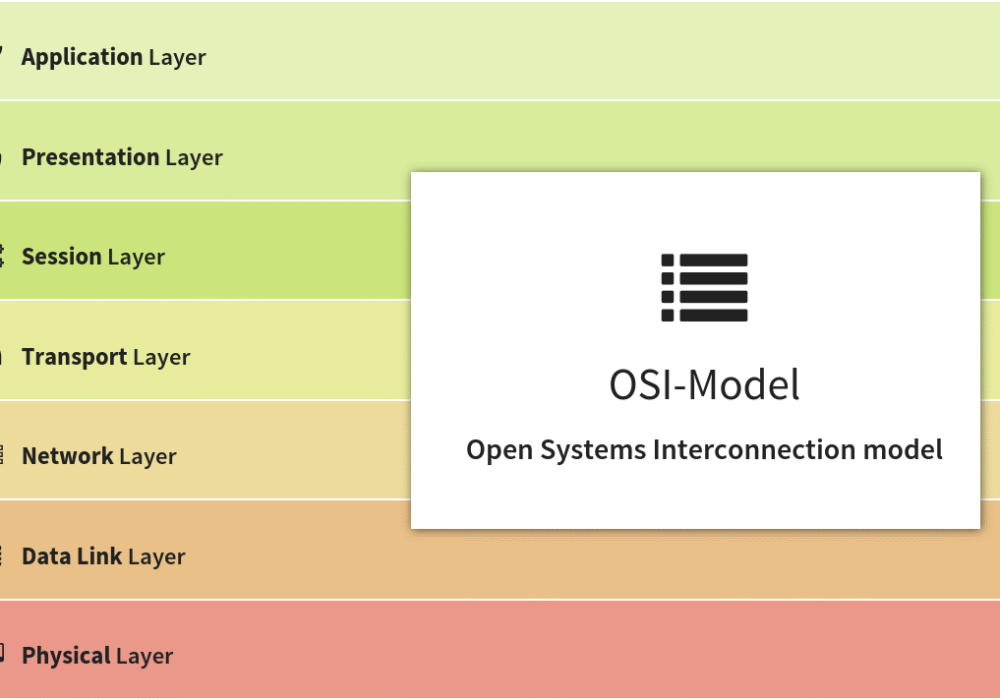
A Layer 3 Network is the third layer of the Open Systems Interconnection (OSI) Model, or network layer....
Read more
January 12th, 2022: Today Microsoft sent a notification of a critical risk to those who use Windows...
Read more
A wave of phishing attacks has been generated within Google's cloud-based word processing solution...
Read more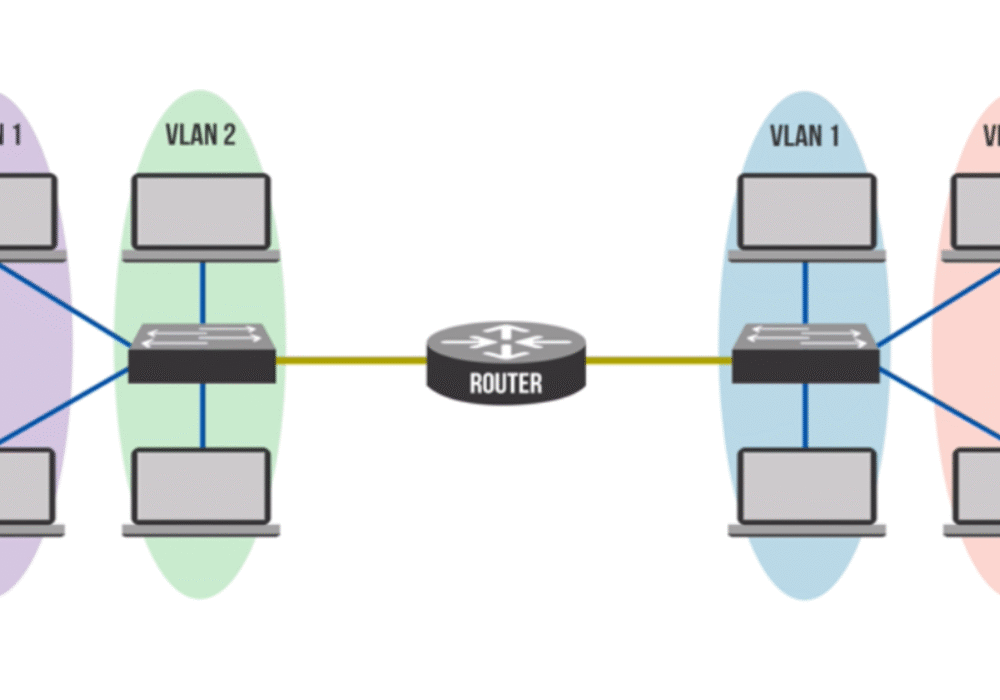
Private Virtual Local Area Network (PVLAN), also known as port isolation, is a network...
Read more
Cybercriminals are always looking for new ways to infiltrate your devices. Recently, they've been using...
Read more
Fleeceware is a malicious application that tricks users into paying money for simple apps with...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
