"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

Secure your business with CyberHoot Today!!! Sign Up Now Fingerprints used in cryptography are short...
Read more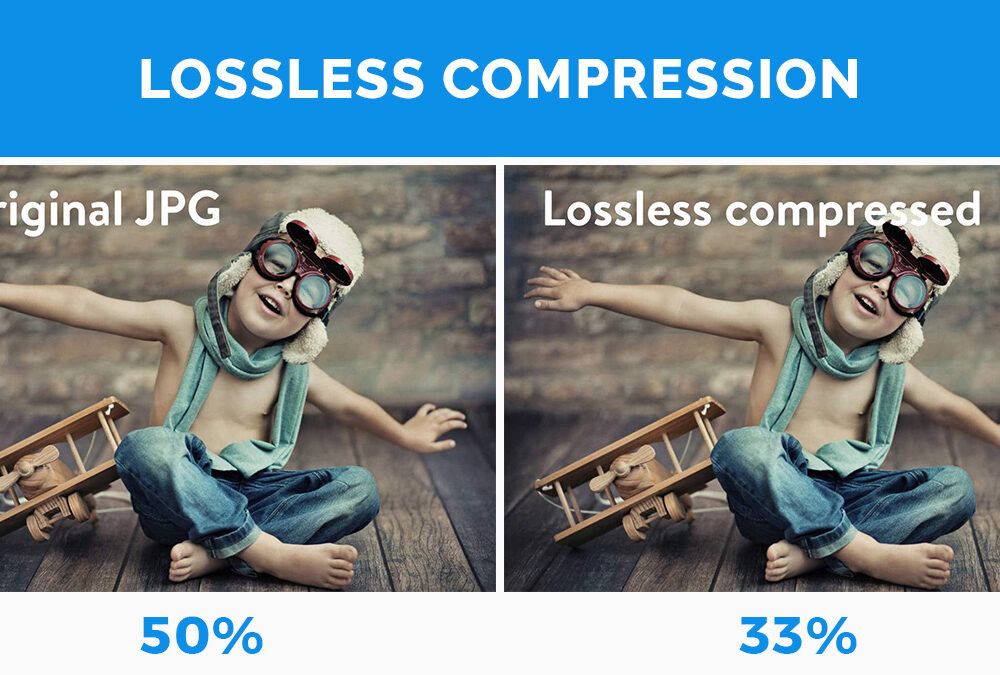
Secure your business with CyberHoot Today!!! Sign Up Now Lossless Compression is when file size is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Lossy Compression is when data is lost or...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now In Mid-February 2022, institutions central...
Read more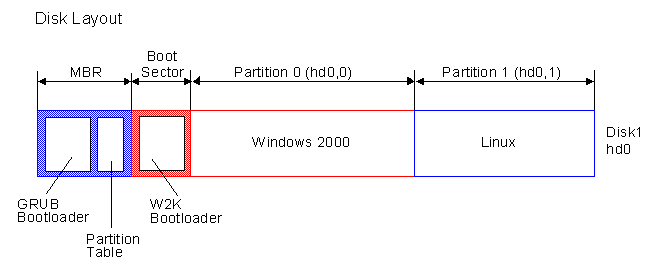
Secure your business with CyberHoot Today!!! Sign Up Now The Master Boot Record (MBR) is the...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Co-Authored by Craig Taylor In an...
Read more
February 18th, 2022: If you’re using PHP in your network, check that you’re using the latest...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Malicious...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Information Disclosure, also known as...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
