"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Last Updated: Sun. March 8th, 2020 The Coronavirus (COVID-19), has infected nearly 90,000 people worldwide as...
Read more
Image Source Risk Analysis is the systematic examination of the components and characteristics of...
Read more
Image Source A Risk Assessment is the product or process which collects information and assigns...
Read more
Image Source Risk Management is the process of identifying, analyzing, assessing, and...
Read more
Image Source Risk-Based Data Management is a structured approach to managing risks to data and information...
Read more
Image Source Risk Acceptance (Accept) refers to accepting the risk that is presented to you or your...
Read more
Image Source Avoidance refers to avoiding the risk that is found altogether. When mitigating risk, there are...
Read more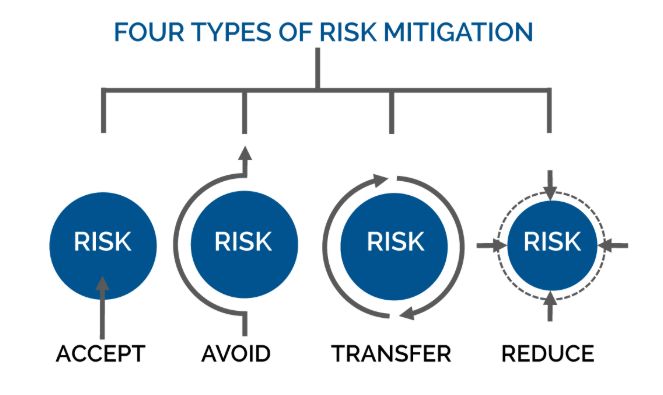
Image Source Mitigation occurs when assessing risk. When assessing risk there are many ways to work...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
