"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Third-Party Risk Management (TPRM) is the process of identifying, assessing, and controlling risks...
Read more
Image Source Integrated Risk Management is the structured approach that enables an enterprise or...
Read more
Image Source Enterprise Risk Management is a comprehensive approach to risk management that...
Read more
Image Source Risk Analysis is the systematic examination of the components and characteristics of...
Read more
Image Source A Risk Assessment is the product or process which collects information and assigns...
Read more
Image Source Risk Management is the process of identifying, analyzing, assessing, and...
Read more
Image Source Risk-Based Data Management is a structured approach to managing risks to data and information...
Read more
Image Source Avoidance refers to avoiding the risk that is found altogether. When mitigating risk, there are...
Read more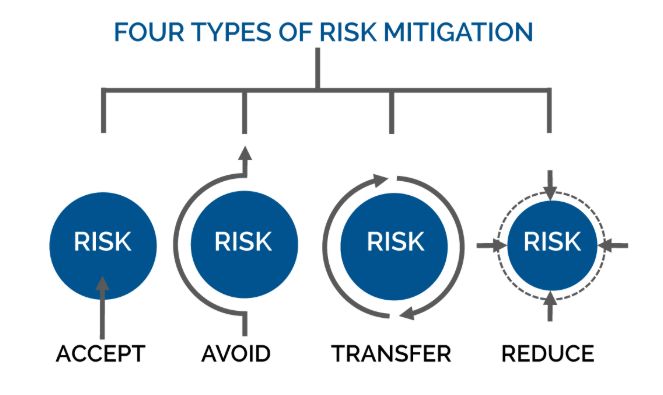
Image Source Mitigation occurs when assessing risk. When assessing risk there are many ways to work...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
