"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."

As many know, the United States had its decennial (every ten years) census in 2020, helping determine...
Read more
Since Instagram's official launch in 2010, it's seen more than 1 billion accounts opened with users...
Read more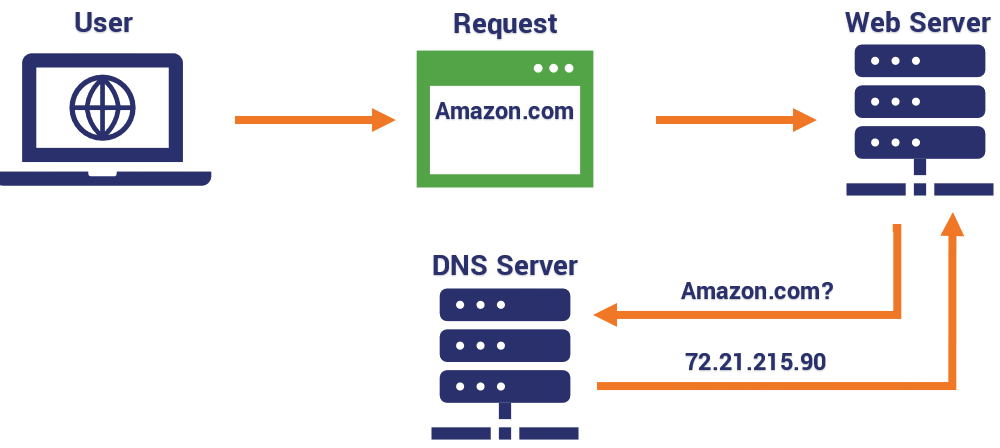
A Domain Name System (DNS) is essentially the 'phonebook' of the Internet. DNS is an elaborate,...
Read more
A PayPal text message phishing campaign was discovered that attempts to steal your account credentials...
Read more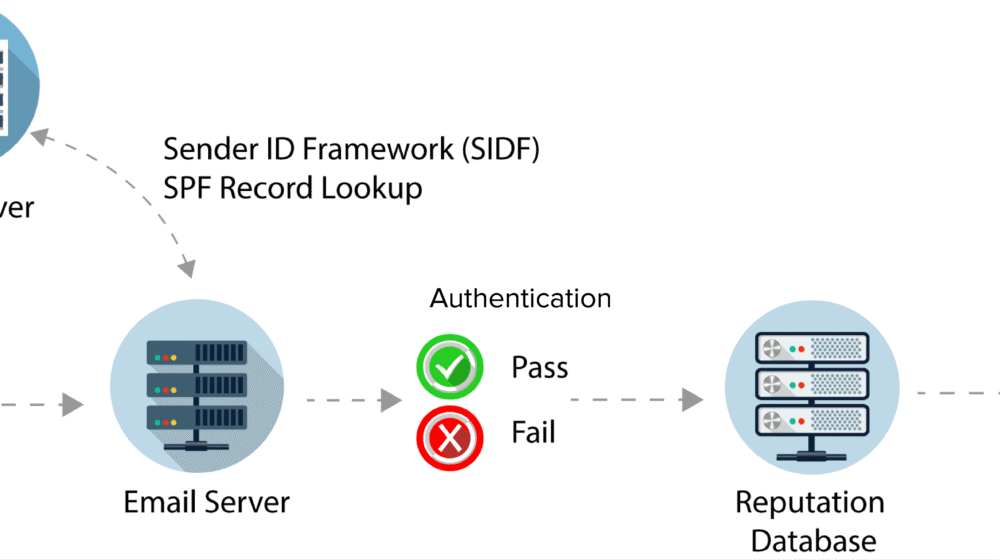
Sender Policy Framework (SPF) is an anti-spam tool where email domains of the senders can be...
Read more
Fake IRS Tax Forms This week, AbnormalSecurity reported an attack on an estimated 15-50 thousand email...
Read more
COVID-19 continues to force companies to deliver their services remotely. A growing threat perhaps...
Read more
Phishing attacks are something that everyone who uses the Internet must be aware of. For those who may...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
