"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
How to Allow-list in AppRiverIf you're using AppRiver's SpamLab spam filtering, you can add CyberHoot to your...
Read more
The holiday shopping season means big business for retailers around the world, but it unfortunately...
Read more
Today is Day Five of Cybersecurity Awareness Month, each day, we will be publishing a video outlining necessary...
Read more
Business Email Compromise (BEC) is when an email account, often in a company's finance department, is...
Read more
Reconnaissance in cybersecurity refers to the preliminary step of a cyberattack, where a hacker is...
Read more
A Malicious URL is a link created with the purpose of promoting scams, attacks, and fraud. By clicking...
Read more
Account Hijacking is where a hacker compromises a computer account that does not belong to them. ...
Read more
Email Impersonation is a form of phishing attack where a hacker impersonates someone else in the hopes it was...
Read more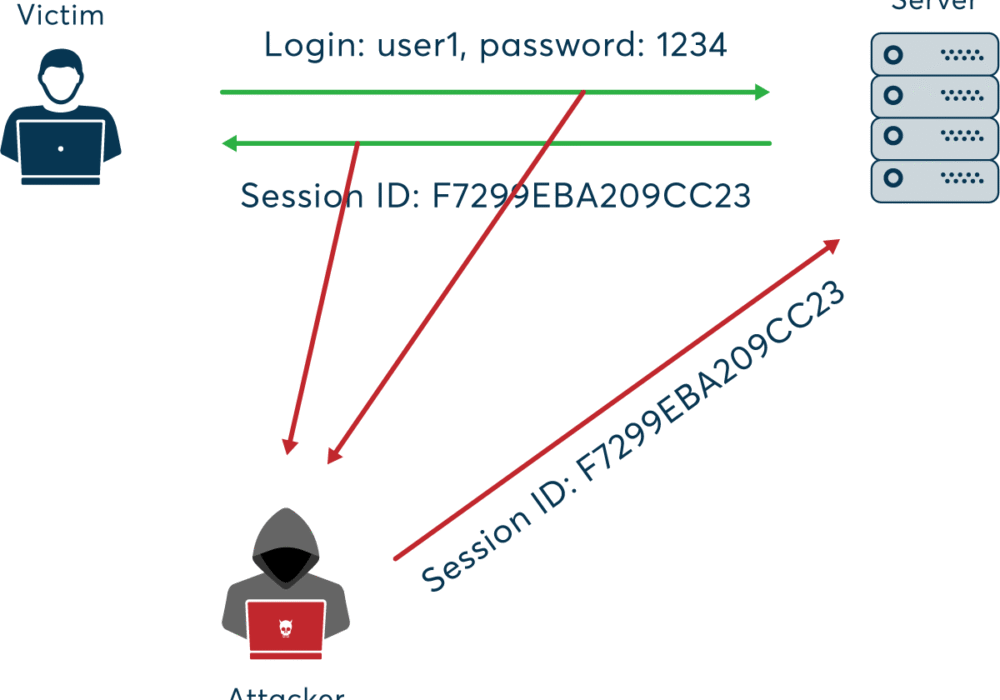
A Session Hijacking Attack occurs when a user session is taken over by an attacker. A normal session...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
