"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."
Threat Hunting is proactive hunting or searching through networks, endpoints, and datasets to find...
Read more
The International Traffic in Arms Regulations (ITAR) is United States regulation that controls the...
Read more
Third-Party Risk Management (TPRM) is the process of identifying, assessing, and controlling risks...
Read more
The Personal Information Protection and Electronic Documents Act (PIPEDA) is Canada's main...
Read more
The General Data Protection Regulation (GDPR) was passed in the European Union (EU) in 2016 and...
Read more
Data Sanitization is the process of permanently and irreversibly destroying data on a storage device in...
Read more
Artificial Intelligence (AI) refers to human-like intelligence presented by a computer, robot, or other...
Read more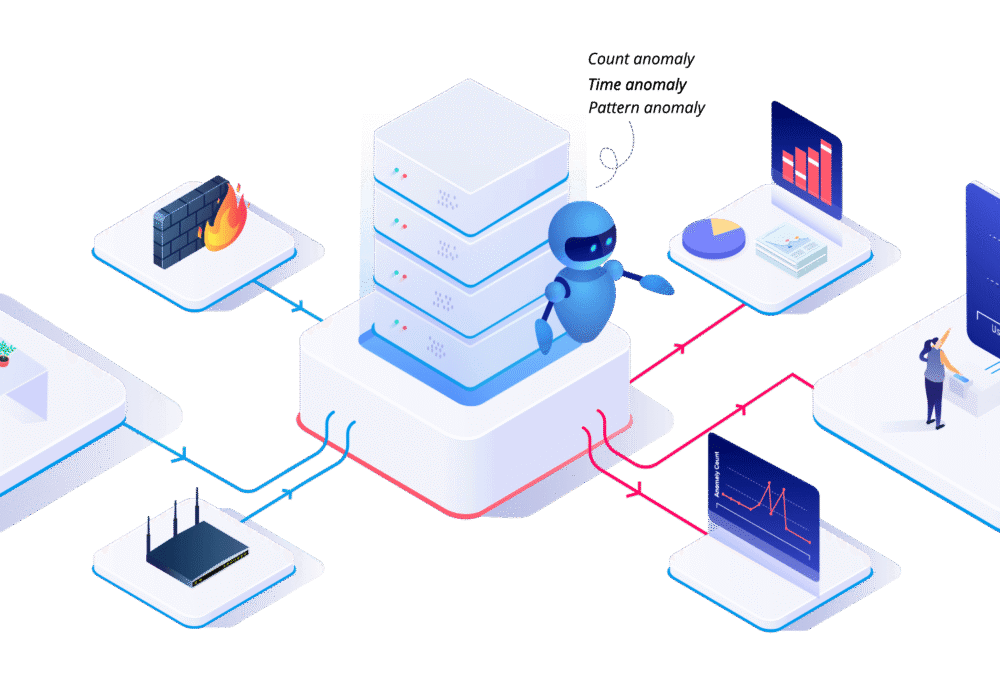
User Behavior Analytics (UBA) is the tracking, collecting, and assessment of user data and activities...
Read more
Non-Fungible Tokens (NFTs) are unique, easily verifiable digital assets that can represent...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
