"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
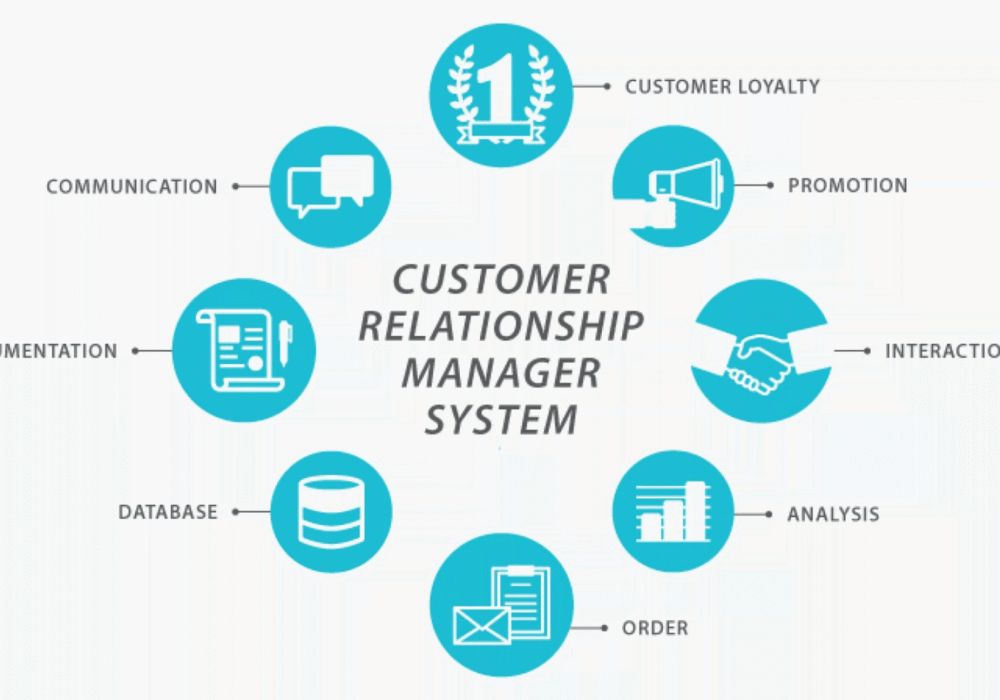
Secure your business with CyberHoot Today!!! Sign Up Now Customer Relationship Management (CRM) is a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Quantum Computing is an area of computing...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Wiper Malware is malicious software that...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Fingerprints used in cryptography are short...
Read more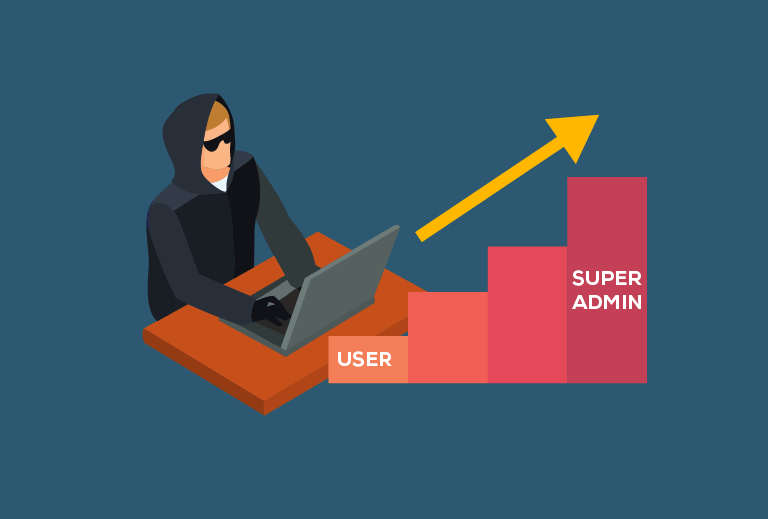
Secure your business with CyberHoot Today!!! Sign Up Now Privilege Escalation Attacks are when...
Read more
An Out-Of-Band (OOB) Patch is a security update released outside of the normal frequency. Typically,...
Read more
Business Email Compromise (BEC) is when an email account, often in a company's finance department, is broken into...
Read more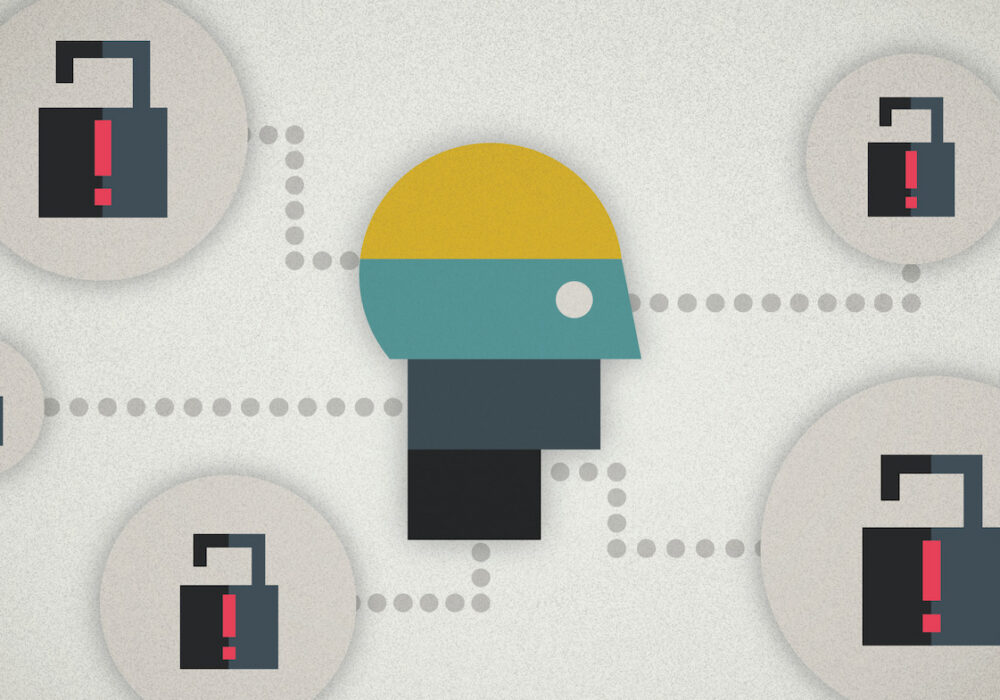
Threat Intelligence (TI) is information about current attack tactics and techniques (T&T) used by...
Read more
Jailbreaking is the exploiting of manufacturer or carrier operating systems, often by removing...
Read more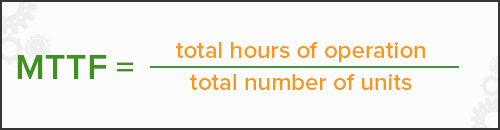
Mean Time to Failure (MTTF) and sometimes references as Mean Time For Failure (MTFF) is the length of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
