"I reviewed over a dozen learning management platforms, and I have to say, CyberHoot is soaring way above the others."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Secure your business with CyberHoot Today!!! Sign Up Now A group of researchers at South Korea's...
Read more
Steganography (pronounced: steh·guh·naa·gruh·fee) is the technique of hiding data secretly within an...
Read more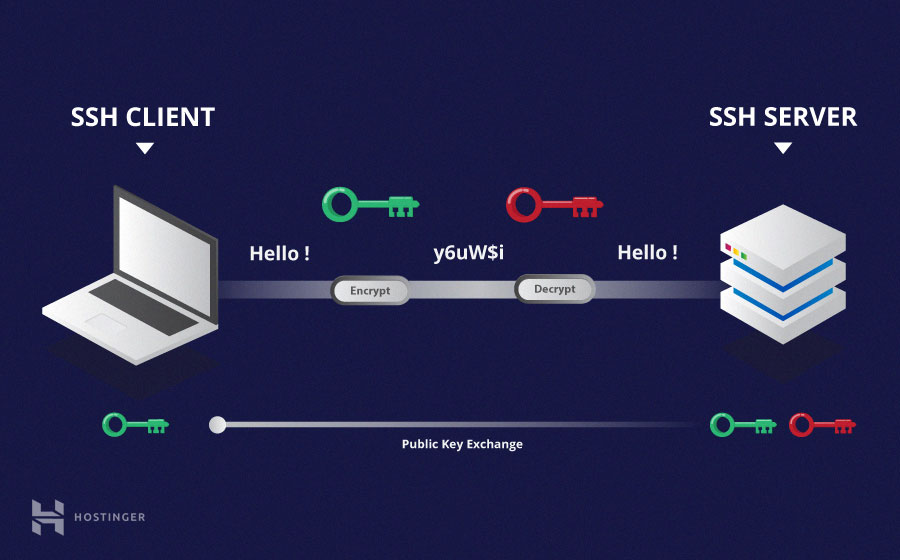
Secure Shell (SSH) is a cryptographic network communications protocol for operating network...
Read more
Image Source Ciphertext is data or information in its encrypted form. Ciphertext is the output when an...
Read more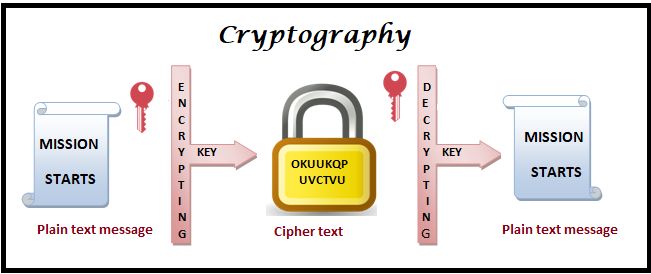
Cryptography is the use of mathematical techniques to provide security services, such as...
Read more
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
Symmetric Cryptography is a branch of cryptography in which a cryptographic system or algorithms use...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
