Wireshark is a free utility that allows network administrators to analyze their network. It’s considered an industry standard utility for network traffic recording and analysis. Wireshark allows administrators to perform packet analysis. Packet analysis is the act of examining individual packets flowing on a network to validate problems, identify attacks, and even check for unencrypted sensitive data.
The Wireshark project was started under the name Ethereal, but was renamed Wireshark in 2006. Network administrators enjoy using Wireshark for its simple interface and many filtering features.
Source: Techopedia, Radware
Additional Reading: Brim Network Forensics Tool Makes Juggling Large Traffic Logs Easy
Related Terms: Packet Analyzer, Packet Sniffing
Possibly. Your Network Administrator had better know about each and every instance of Wireshark on your network. Wireshark’s powerful packet assembly capabilities make it a staple in a hacker toolkit in addition to Network Administrators. It is very useful for finding plaintext passwords floating by on unencrypted protocols on your Local Area Network. Therefore, if you find a compromised host on your network and Wireshark was installed on that host recently, you may have a significant problem on your hands.
Most Managed Service Providers will need a seasoned network engineer who can perform network analysis with Wireshark on staff to identify critical bandwidth problems, poor application performance issues, and the root cause of networking issues. This is one of the many benefits of working with Managed Services Providers on your IT infrastructure for IT planning, IT troubleshooting, and vendor management.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read more
Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read more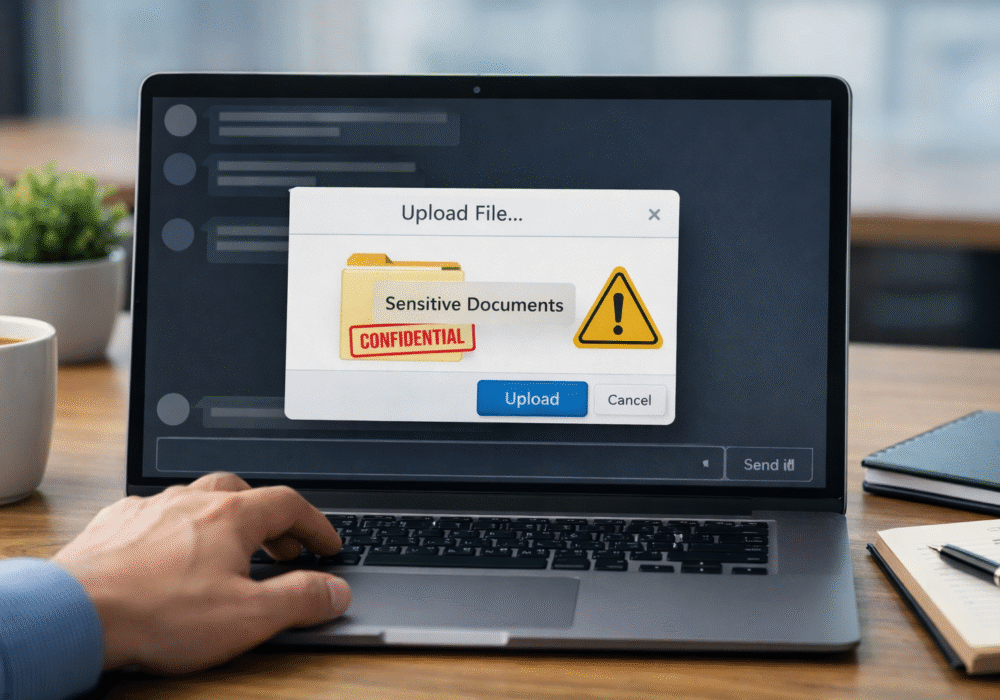
Not surprising when Trouble Ensues Last summer, the interim head of a major U.S. cybersecurity agency uploaded...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
