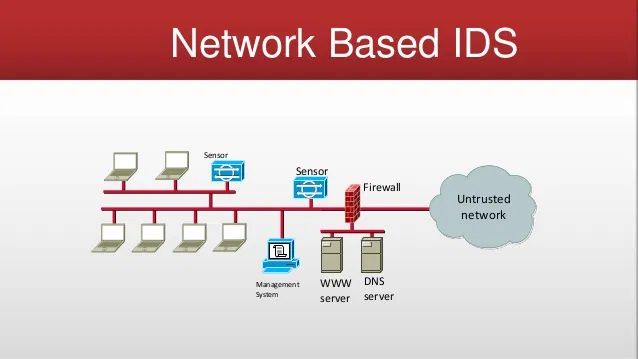
A Network Based Intrusion Detection System (NIDS), or Network Based IDS, is security hardware that is placed strategically to monitor critical network traffic. Traditional Network Based IDS analyzes passing network traffic and matches that traffic to a library of known attacks in its system. Newer systems use artificial intelligence (aka heuristics) to analyze traffic for patterns of interest. When an attack is identified, or a pattern of interest is found, an alert is sent typically to a Security Operations Center (aka: SOC) who review the alert and triage it for validity and subsequent escalation.
Source: Wiki Network Intrusion Detection Systems
Related Terms: Packet Sniffing, Intrusion Prevention Systems
Network Intrusion Detection Services is an advanced and expensive proposition for it to work properly and effectively within a company’s environment. It is often used in Data Centers with Cloud Hosting providers to provide a higher level of cybersecurity assurance on their critical networks. However, in the SMB arena, it is often too expensive to be practical. Additionally, it provides security services that would only be appropriate if all your Level 1, 2, and 3 cybersecurity maturity services, processes, and policies were in place. Most SMB’s are not operating with this level of maturity. Therefore, I seldom recommend IDS or its more expensive relative IPS (Intrusion Prevention Services) in the SMB network space. Exceptions to this general guidance do apply, especially within regulated industries in high finance, defense contractors seeking high level certifications for example.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
