
Email Impersonation is a form of phishing attack where a hacker impersonates someone else in the hopes it was convince an employee to act in some fashion.
Email impersonation attacks often use senior company executives such as the CEO or CFO to make an initial email inquiry. Sometimes it will be worded like this:
Jane, heading into a meeting, are you busy? John
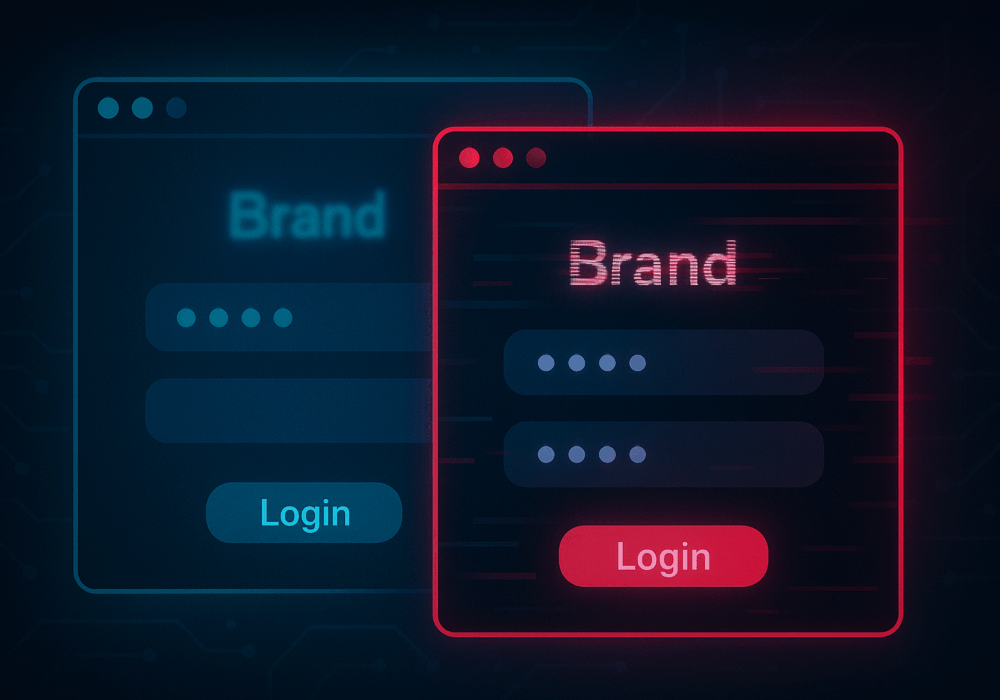
The sender name looks like the senior person in your organization and at first glance might be indistinguishable from the real person. These emails always ask the victims to perform a task, urgently. Examples of such attacks include purchasing gift cards, sending personel records or W2’s, or logging into a website to retrieve a critical file for the CEO/CFO. In each case, the real sender is a hacker impersonating that Very Important Person (VIP).
Impersonation emails are a common form of social engineering to be on the lookout for. They are easy to complete using public information from the corporate website and very difficult to prevent from delivery.
Source: Barclays Corporate Banking
Additional Reading: What is Business Email Compromise?
Related Terms: Phishing, Spear-Phishing, Whaling
SMBs are big targets for phishing attacks, as attackers know that SMBs tend to lack the resources available to defend against them. The good news is that phishing attacks are one of the easiest topics to train employees on how to spot and avoid. Follow these best practices to reduce your likelihood of being breached by a phishing attack, especially impersonation-based attacks.
https://youtube.com/watch?v=PszKH3fbWzg
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
In cybersecurity, not all attacks happen through fancy malware or zero-day exploits. Some of the most effective...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
