"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
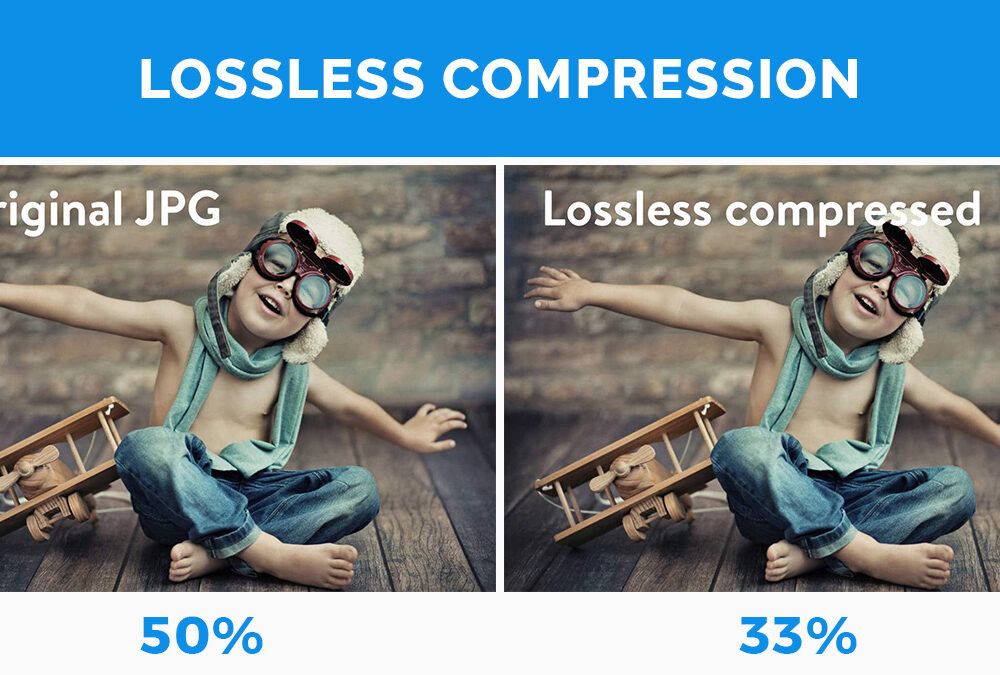
Secure your business with CyberHoot Today!!! Sign Up Now Lossless Compression is when file size is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Lossy Compression is when data is lost or...
Read more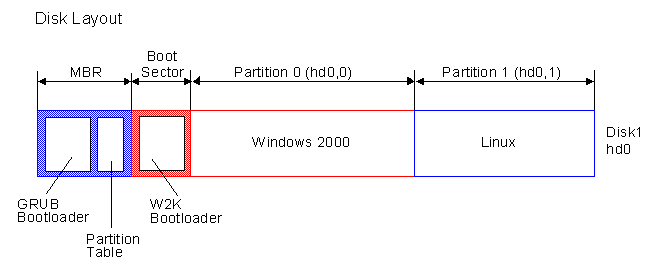
Secure your business with CyberHoot Today!!! Sign Up Now The Master Boot Record (MBR) is the...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Information Disclosure, also known as...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Privilege Escalation Attacks are when...
Read more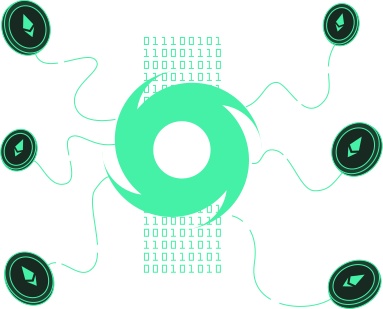
Secure your business with CyberHoot Today!!! Sign Up Now Tornado Cash is an Ethereum (ETH) mixer...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Remote Code Execution (RCE) is an attack...
Read more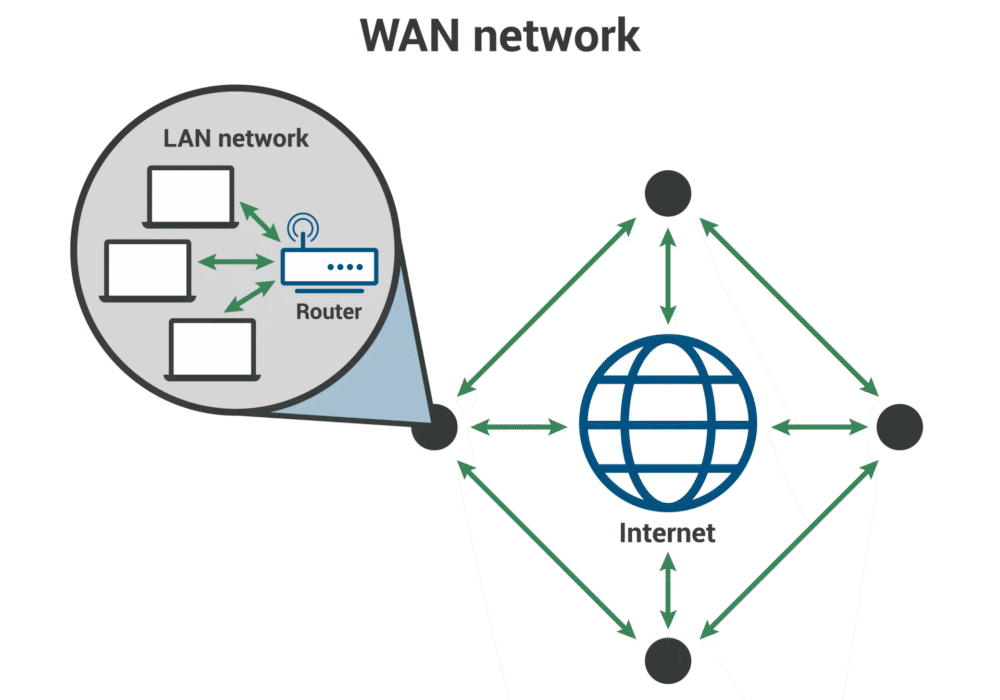
Secure your business with CyberHoot Today!!! Sign Up Now A Wide Area Network (WAN) is a large...
Read more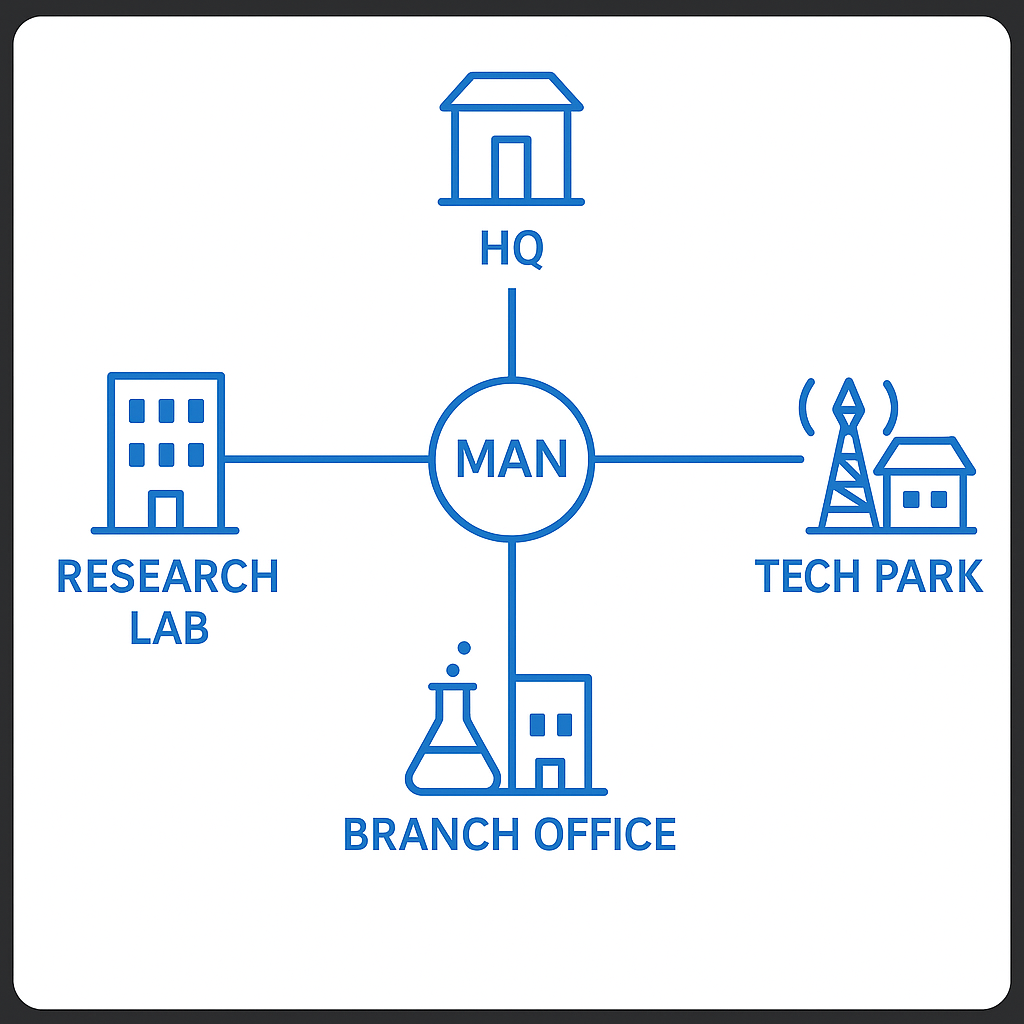
Secure your business with CyberHoot Today!!! Sign Up Now A Metropolitan Area Network (MAN) is a...
Read more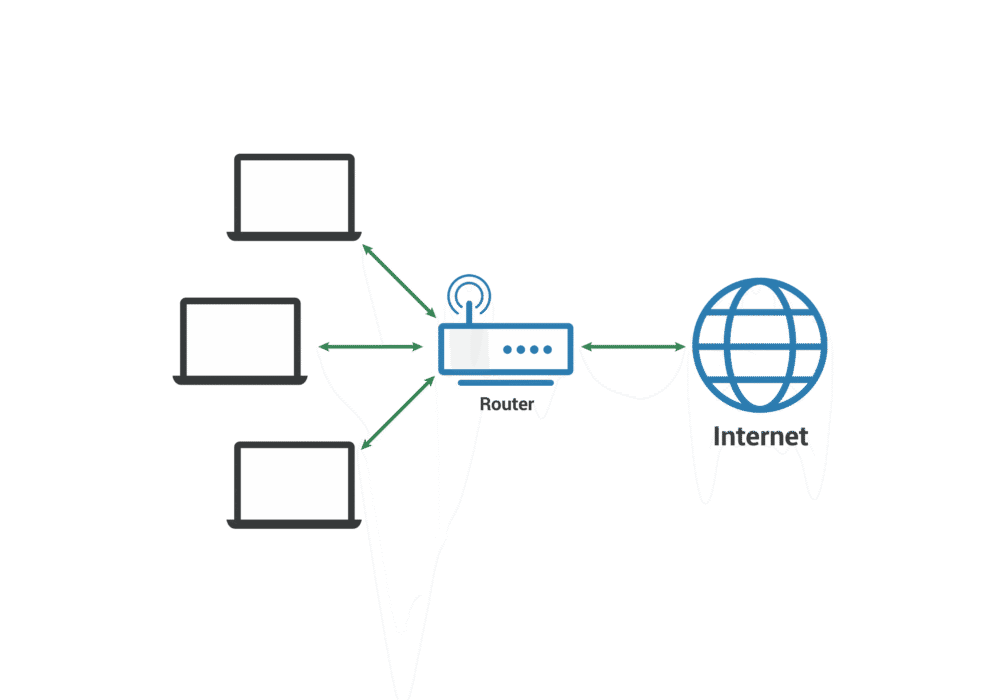
Secure your business with CyberHoot Today!!! Sign Up Now A Local Area Network (LAN) is a group of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Error Detection in cybersecurity refers to...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
