"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
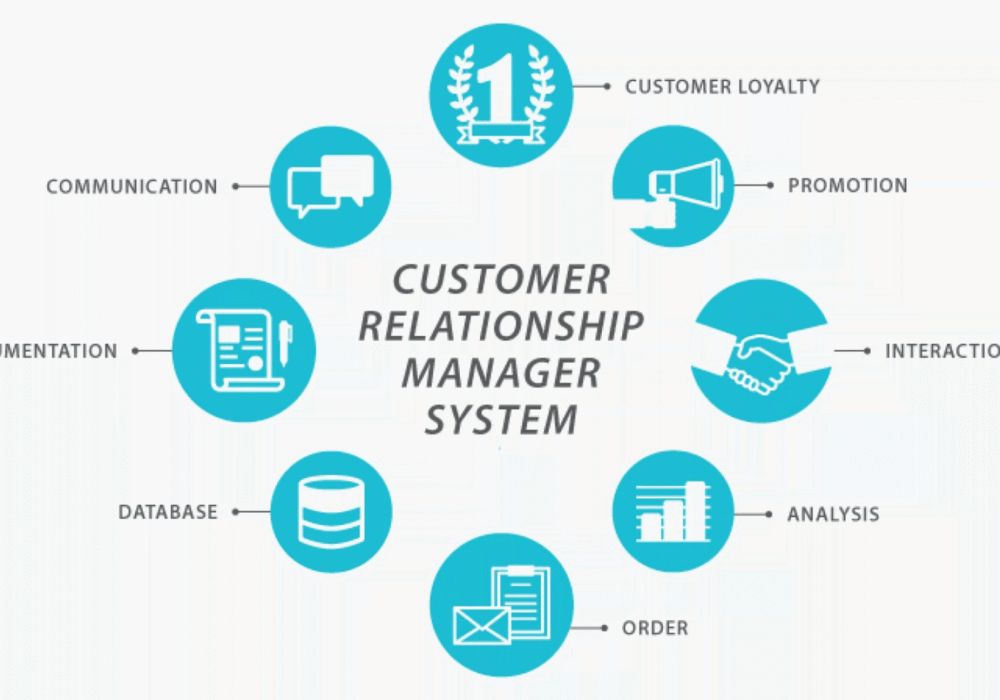
Secure your business with CyberHoot Today!!! Sign Up Now Customer Relationship Management (CRM) is a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Enterprise Resource Planning (ERP) is a...
Read more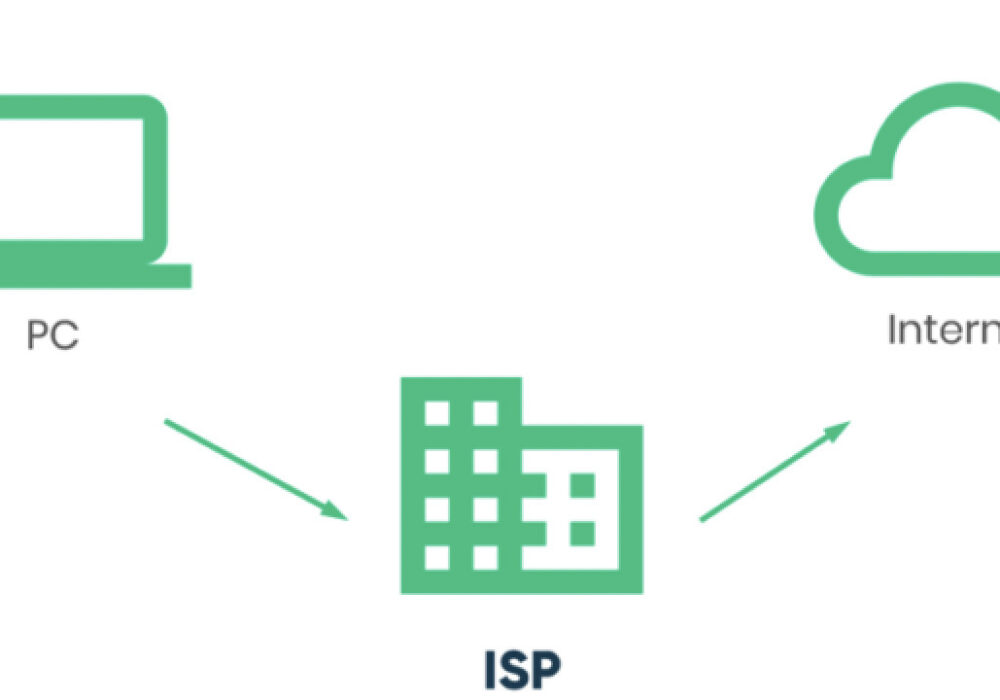
Secure your business with CyberHoot Today!!! Sign Up Now An Internet...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Emergency Data Request (EDR) is a...
Read more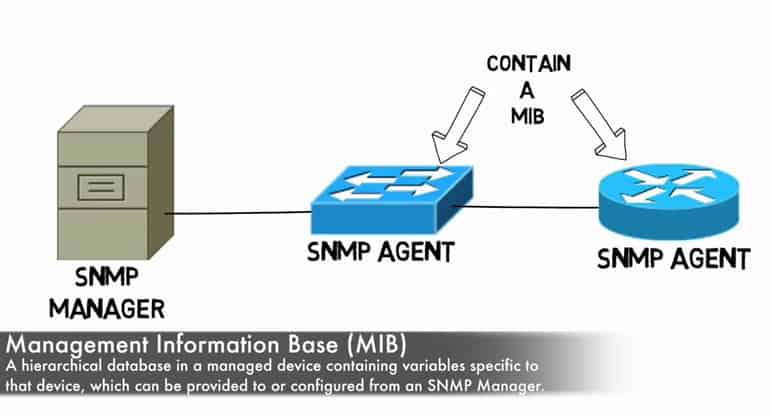
Secure your business with CyberHoot Today!!! Sign Up Now A Management Information Base...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Network Management System (NMS) is an...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Self Assessment Questionnaire...
Read more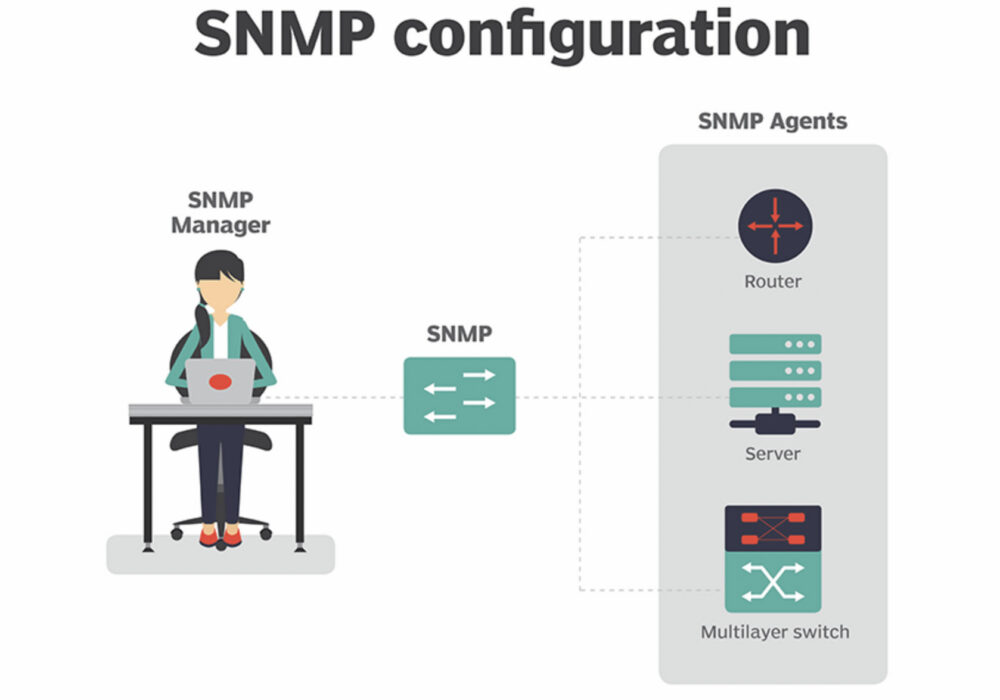
Secure your business with CyberHoot Today!!! Sign Up Now Simple Network Management Protocol...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Error correction code (ECC) checks read...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Quantum Computing is an area of computing...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Moore’s Law is a 1965 observation made by...
Read more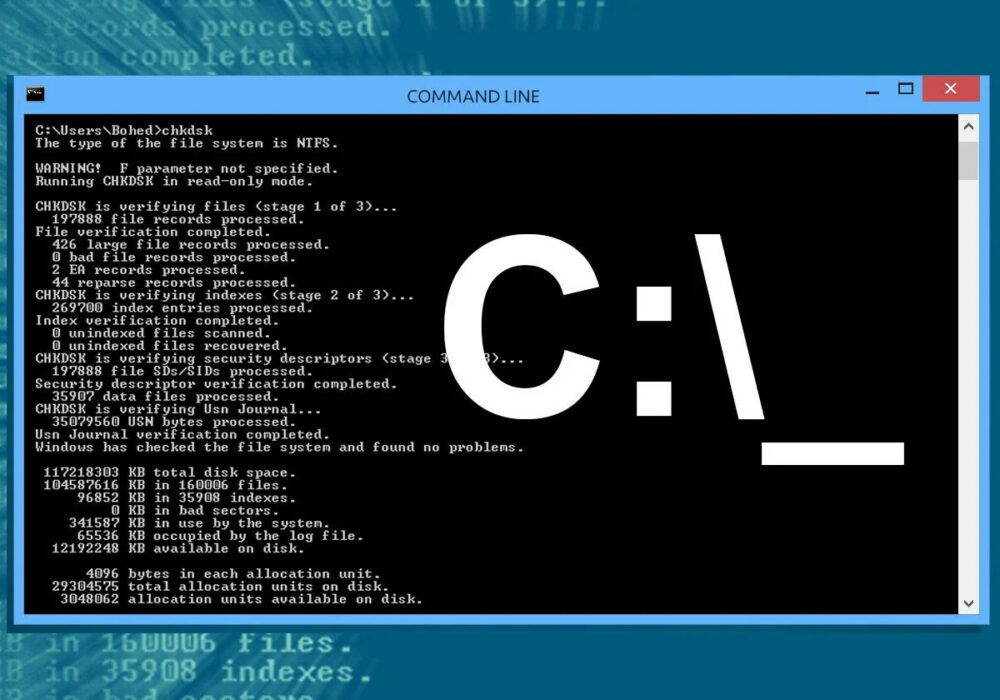
Secure your business with CyberHoot Today!!! Sign Up Now A Command Line Interface (CLI) is a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
